A newly identified threat activity cluster has been linked to an ongoing malicious campaign that has targeted U.S. education and healthcare organizations since at least December 2025.
Cisco Talos is tracking this activity under the designation UAT‑10027. The attackers’ primary objective is to deploy a previously unseen backdoor named Dohdoor.
According to security researchers Alex Karkins and Chetan Raghuprasad, who shared their findings with The Hacker News, “Dohdoor leverages DNS‑over‑HTTPS (DoH) for its command‑and‑control (C2) operations and is capable of reflectively loading and executing additional payload binaries.”
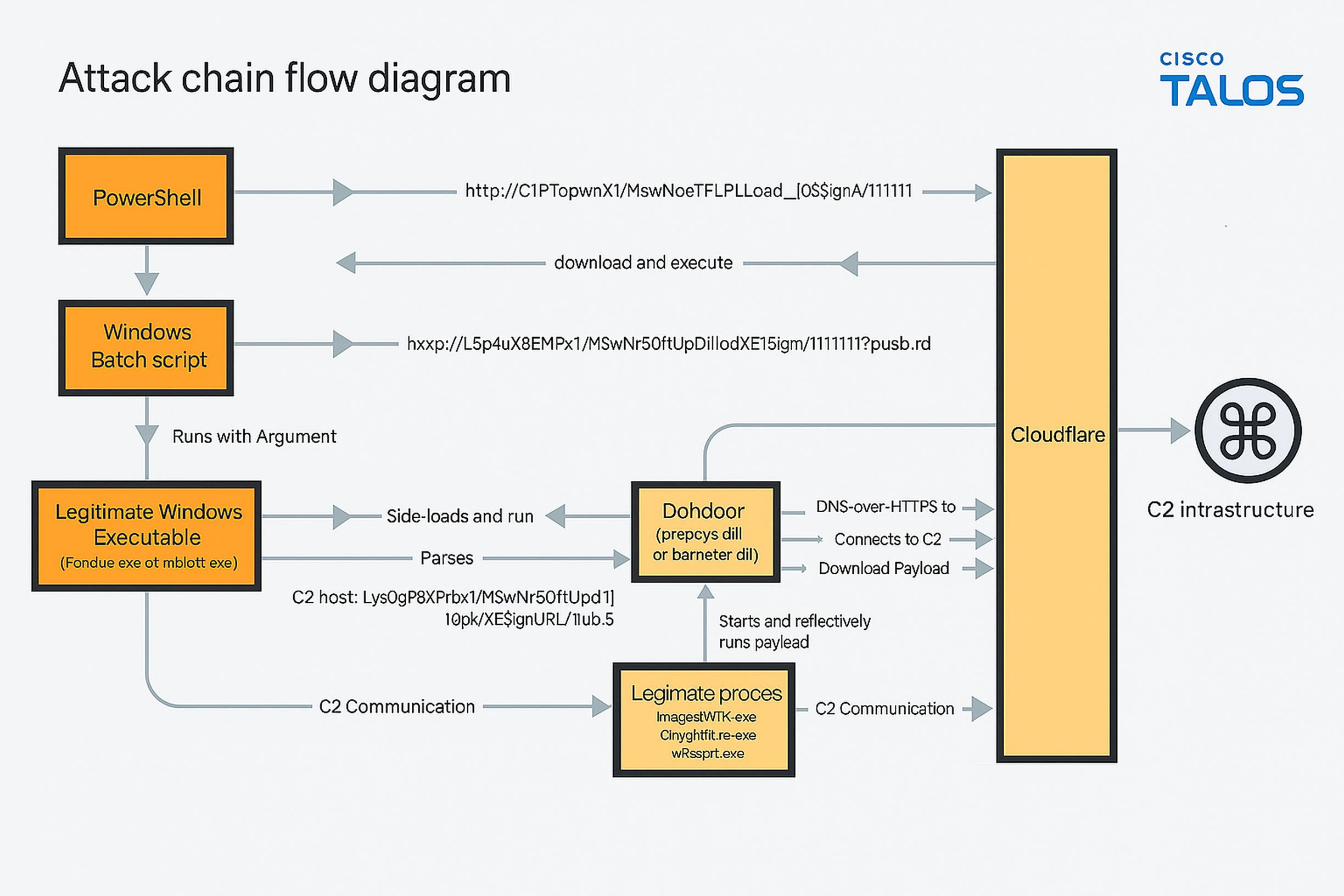
While the initial entry vector has not yet been determined, investigators believe the attackers likely rely on socially engineered phishing emails. These lead victims to execute a PowerShell script that downloads and runs a Windows batch file from a remote staging server. That file then retrieves a malicious Windows DLL named “propsys.dll” or “batmeter.dll” from the same server.
This DLL, representing the Dohdoor payload, is executed via DLL sideloading through legitimate Windows executables such as Fondue.exe, mblctr.exe, or ScreenClippingHost.exe. Once activated, the backdoor enables the delivery of an additional in‑memory payload, assessed to be a Cobalt Strike Beacon.
Talos noted that the threat actor conceals its C2 infrastructure behind Cloudflare services, ensuring that victim traffic appears as normal HTTPS communication toward trusted Cloudflare IPs. This approach evades DNS‑based detection mechanisms, DNS sinkholes, and traffic inspection systems that rely on monitoring suspicious domain queries allowing the malware’s C2 communications to remain hidden.
Dohdoor also unhooks system calls to evade endpoint detection and response (EDR) tools that monitor Windows API usage through user‑mode hooks in NTDLL.dll.
Raghuprasad told The Hacker News that multiple educational institutions including a university connected to several others were compromised, suggesting a potentially broad attack surface. One impacted organization was a healthcare facility providing elderly care. So far, investigators have found no evidence that data has been exfiltrated. Although the only observed follow‑on payload is the Cobalt Strike Beacon, researchers believe UAT‑10027 may be financially motivated based on the nature of the victims.
Attribution remains unclear, but Cisco Talos observed operational resemblances between Dohdoor and LazarLoader, a downloader previously tied to North Korea’s Lazarus Group in campaigns targeting South Korea.
Talos concluded that although certain technical features resemble Lazarus tooling, the campaign’s focus on the education and healthcare sectors differs from Lazarus’ typical targets, which often include cryptocurrency and defense industries.
However, Talos also noted that other North Korean APTs have previously targeted these sectors for example, the Maui ransomware attacks against healthcare organizations and Kimsuky’s operations involving academic institutions reflecting some overlap between UAT‑10027’s victim profile and known North Korean threat groups.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.



