Google announced on Wednesday that it partnered with industry collaborators to dismantle the infrastructure of a suspected China‑linked cyber espionage group known as UNC2814, which had compromised at least 53 organizations across 42 countries.
According to a report from the Google Threat Intelligence Group (GTIG) and Mandiant, UNC2814 is a prolific and highly evasive threat actor with a long history of targeting government entities and major telecommunications organizations throughout Africa, Asia, and the Americas. Google further noted that the group may be responsible for additional intrusions spanning more than 20 other countries. The company has tracked UNC2814 since 2017, observing the group’s use of API-based communication with SaaS platforms to disguise command‑and‑control (C2) traffic as legitimate software activity.
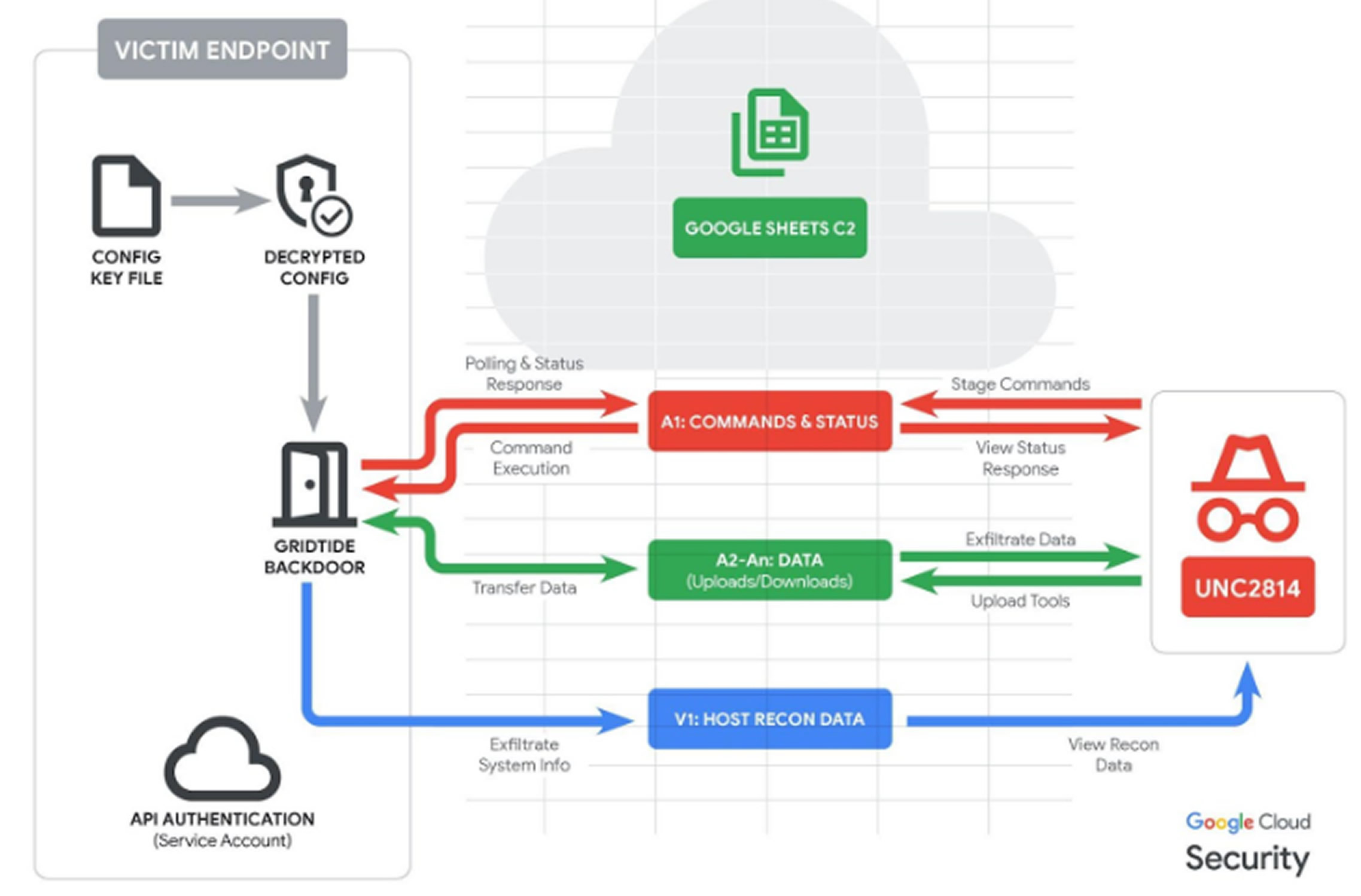
At the core of UNC2814’s operations is GRIDTIDE, a newly identified backdoor that leverages the Google Sheets API as a covert communication channel. By embedding commands and exfiltrated data in spreadsheet cells, the malware mimics normal web analytics traffic. GRIDTIDE, developed in C, supports file transfers, execution of arbitrary shell commands, and other remote administrative actions.
The method by which UNC2814 gains initial access remains under investigation, though the group has frequently been observed exploiting vulnerable web servers and edge appliances. Once inside a network, UNC2814 uses a service account to move laterally over SSH and relies on “living‑off‑the‑land” (LotL) binaries to perform reconnaissance, escalate privileges, and establish persistence. As part of maintaining persistence, attackers created a malicious service at /etc/systemd/system/xapt.service, which launches the malware from /usr/sbin/xapt.
Another notable technique includes deploying SoftEther VPN Bridge to create outbound encrypted tunnels—an approach previously associated with multiple Chinese threat groups. Google noted that GRIDTIDE was often found on systems containing personally identifiable information (PII), consistent with espionage objectives, although no direct data exfiltration was observed during this campaign.
GRIDTIDE’s C2 design uses a specific cell‑based polling structure within Google Sheets:
- A1 – polls for attacker commands and is overwritten with status codes (e.g., S‑C‑R, “Server‑Command‑Success”)
- A2–An – stores command output and transferred files
- V1 – contains system metadata from the compromised endpoint
In response to these intrusions, Google terminated all attacker‑controlled Google Cloud Projects, disabled known UNC2814 infrastructure, and cut off access to the accounts and Google Sheets API calls used for C2 communications. Google described UNC2814 as one of the most expansive and significant intrusion campaigns it has confronted in recent years. The company has notified all identified victims and is assisting organizations with confirmed breaches.
This campaign is part of a broader trend involving Chinese state‑aligned groups embedding themselves deeply within networks for long‑term espionage. It also underscores the persistent exploitation of the network edge, where appliances often lack endpoint detection and yet provide a direct pivot into internal systems. Such devices have become high‑value targets due to weak defenses and their critical role in enterprise architecture.
Google noted that UNC2814’s activities confirmed or suspected in more than 70 countries—demonstrate the significant threat posed to telecommunications and government sectors. The company added that campaigns of this reach typically result from years of sustained effort, and despite the disruption, it expects UNC2814 will attempt to re‑establish its global presence.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.



