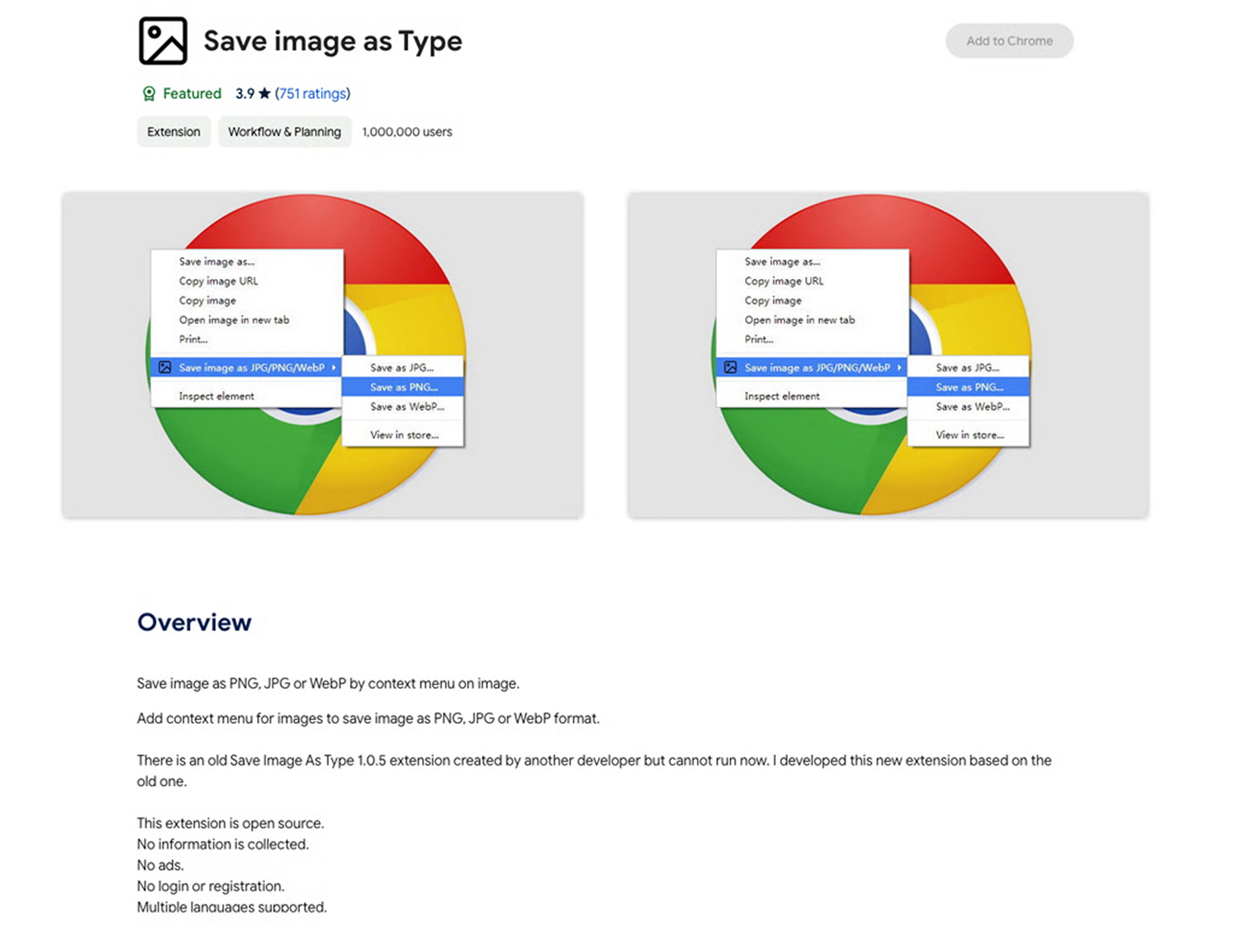
A widely used Chrome extension that was previously promoted by Google and downloaded more than one million times, was quietly transferred to new ownership and later updated with malicious functionality designed to siphon affiliate commissions from hundreds of online retailers, according to a report by XDA.
The fraudulent behavior works by overwriting affiliate cookies, meaning legitimate affiliates may never receive commissions they rightfully earned after referring customers.
Google has since flagged and disabled the extension, preventing it from running for more than a million users. Its Chrome Web Store listing now displays a notice stating that the item is no longer available. The issue was uncovered by Adam Conway, XDA’s Lead Technical Editor and a former user of the extension who discovered that the add‑on had been stealthily modified with malicious code sometime in 2025.
“What I uncovered was an affiliate fraud operation that had been running in my browser for months,” Conway said. “It was silently injecting hidden iframes into nearly every website I visited to plant affiliate cookies for over a thousand different merchants.”
How the Fraud Worked
According to Conway’s analysis, the malicious logic was intentionally engineered to evade detection. The code only activated after a user had saved at least 10 images, delaying execution to avoid immediate suspicion. Once triggered, the extension injected hidden iframes into web pages for roughly 8.5 seconds before removing them.
To further reduce the risk of discovery, the extension deliberately avoided executing on developer‑focused websites, where technically savvy users might inspect page behavior. Conway ultimately identified nearly 600 unique affiliate redirect URLs stored locally, all tied to an affiliate redirection service called Karmanow.
A Broader Pattern of Abuse
After examining the extension’s source code, Conway said the incident has permanently changed how he views browser utilities. “I’ll be far more skeptical of utility extensions going forward,” he noted.
Security experts warn this case is not an isolated incident. Researcher Wladimir Palant has previously documented a larger ecosystem of malicious Chrome extensions engaged in affiliate fraud, linking at least 12 compromised extensions to Karma Shopping Ltd., an Israeli company associated with similar practices.
While cookie hijacking may appear relatively harmless at first glance, it carries broader implications. The technique can be used to track browsing and purchasing behavior, distort attribution models, and financially harm reviewers, bloggers, creators, and small affiliates who rely on legitimate commission revenue.
Why This Matters
More concerning is the fact that browser extensions once trusted can be updated at any time with entirely new functionality. In this case, the malicious code was limited to affiliate fraud, but security researchers caution that the same mechanism could just as easily be used to deliver far more dangerous payloads, potentially leading to full system compromise if left undetected.
Researchers have demonstrated that even Chrome extensions with minimal or no special permissions can manipulate downloaded files, appending malicious commands that facilitate malware delivery—highlighting the outsized risk posed by compromised extensions.
Takeaway
The incident underscores a critical reality for users and organizations alike: popularity and prior trust are not guarantees of safety. Silent ownership changes, delayed activation techniques, and cleverly hidden logic make browser extensions an increasingly attractive attack surface for fraud and malware campaigns.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.