Ukrainian organizations have become the focus of a newly identified cyber‑espionage campaign that researchers believe is likely tied to Russia‑aligned threat actors, according to findings from S2 Grupo’s LAB52 threat intelligence unit.
The activity, observed in February 2026, shows notable similarities to an earlier operation attributed to Laundry Bear also tracked as UAC‑0190 or Void Blizzard which previously targeted Ukrainian defense entities using the PLUGGYAPE malware family.
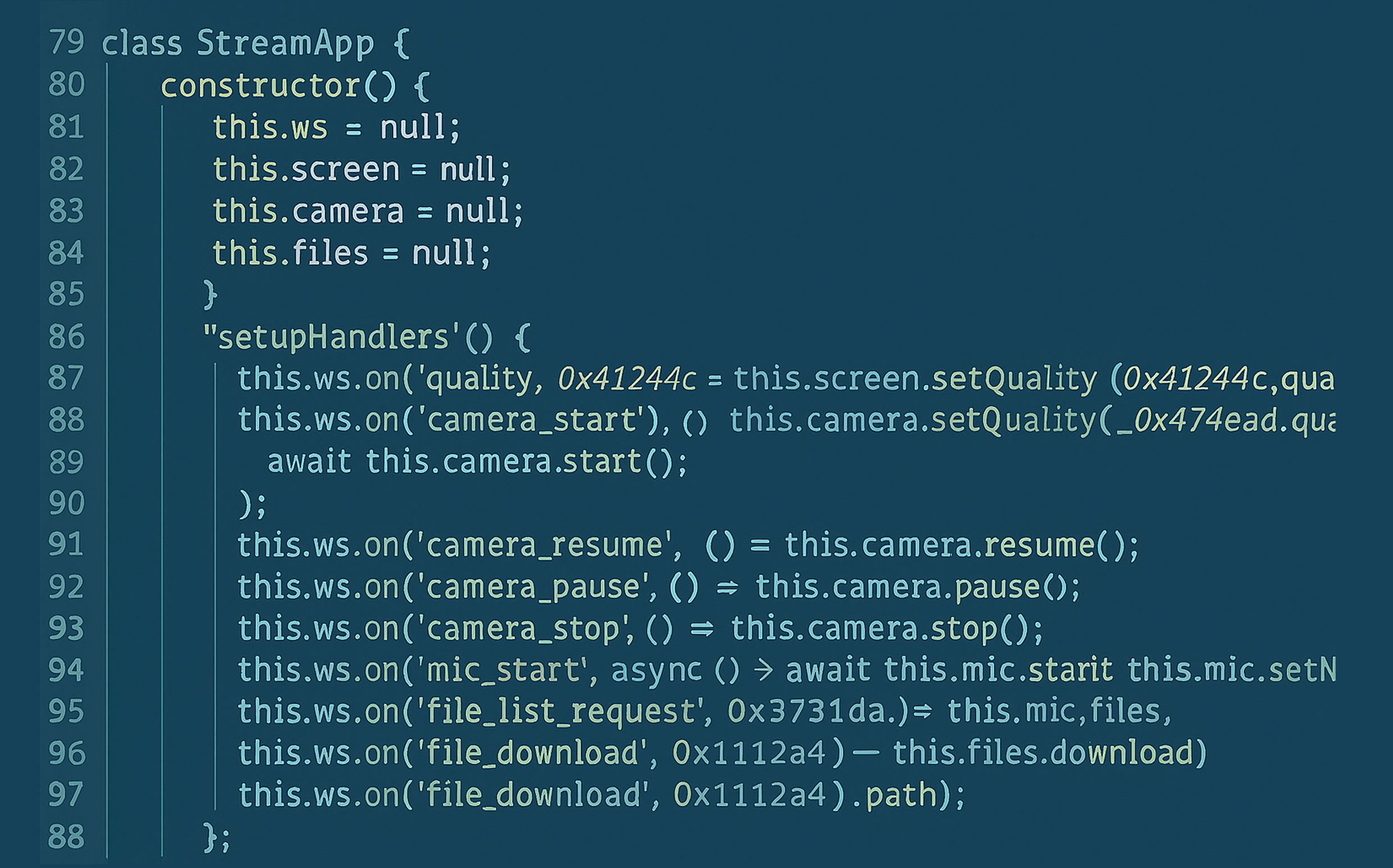
According to LAB52, the attackers are using legal‑ and charity‑themed social‑engineering lures to deploy a JavaScript‑based backdoor that operates entirely through the Microsoft Edge browser. The malware, dubbed DRILLAPP, supports file upload and download capabilities, microphone access, and webcam image capture by abusing legitimate browser functionality
Initial Infection and Execution Flow
Researchers identified two distinct variants of the campaign.
The first version, detected in early February 2026, relies on Windows shortcut (LNK) files. When opened, the LNK file creates an HTML Application (HTA) in the system’s temporary directory, which then retrieves a remote JavaScript payload hosted on Pastefy, a legitimate paste‑hosting service.
To maintain persistence, the attackers copy the LNK files into the Windows Startup folder, ensuring the payload executes automatically after a reboot. As part of the infection chain, victims are shown URLs themed around Starlink installation or a well‑known Ukrainian charity, the Come Back Alive Foundation, to reinforce the legitimacy of the lure.
The HTA file is ultimately executed using Microsoft Edge in headless mode, which loads the obfuscated JavaScript from Pastefy.
Abuse of Microsoft Edge Debugging Features
Edge is launched with a series of permissive command‑line flags, including:
--no-sandbox--disable-web-security--allow-file-access-from-files--use-fake-ui-for-media-stream--auto-select-screen-capture-source=true--disable-user-media-security
These parameters allow the browser to access the local file system, microphone, camera, and screen‑capture features without user interaction or consent.
In effect, DRILLAPP operates as a lightweight browser‑based backdoor, enabling attackers to enumerate files, capture audio and video, and take screenshots—all from within a process that typically appears benign.
Fingerprinting, Targeting, and C2 Communication
On first execution, the malware generates a unique device fingerprint using canvas fingerprinting. It then uses Pastefy as a dead‑drop resolver to retrieve a WebSocket‑based command‑and‑control (C2) endpoint.
The backdoor transmits the fingerprint along with the victim’s geographic location, inferred from the system’s time zone. The malware explicitly checks for time zones associated with:
- United Kingdom
- Russia
- Germany
- France
- China
- Japan
- United States
- Brazil
- India
- Ukraine
- Canada
- Australia
- Italy
- Spain
- Poland
If the time zone does not match any of these regions, it defaults to the United States.
Second Campaign Variant
A second iteration, observed in late February 2026, replaces LNK files with Windows Control Panel (.CPL) modules while preserving much of the original execution logic.
This newer version also enhances the backdoor’s functionality, adding support for:
- Recursive directory traversal
- Bulk file uploads
- Arbitrary file downloads
Because JavaScript cannot natively download files from remote sources, LAB52 noted that the attackers leverage the Chrome DevTools Protocol (CDP)—an internal Chromium debugging interface that becomes available when the browser is launched with the --remote-debugging-port flag.
Development Status and Early Variants
Researchers believe DRILLAPP remains under active development. An earlier variant detected in the wild on January 28, 2026, was observed communicating only with the domain gnome[.]com, rather than pulling its main payload from Pastefy.
LAB52 highlighted the campaign’s reliance on the browser as a particularly noteworthy tactic.
“One of the most striking aspects of this operation is the decision to deploy the backdoor through a web browser, suggesting the attackers are experimenting with new detection‑evasion techniques,” the researchers said.
They added that browsers offer several advantages to attackers: they are ubiquitous and typically trusted processes, expose powerful capabilities via debugging features that enable unsafe actions, and provide legitimate access to sensitive resources such as microphones, cameras, and screen recording—without immediately triggering security alerts.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.



