The second day of Pwn2Own Berlin 2026 saw researchers earn an additional $385,750 for uncovering 15 previously unknown vulnerabilities. This brings the event’s total bounty to $908,750 and 39 unique zero-day flaws discovered across the first two days, with one day still remaining in the competition.
Participants successfully demonstrated exploits targeting widely deployed platforms such as Windows 11, Microsoft Exchange, and Red Hat Enterprise Linux for Workstations. These results underscore the continued presence of exploitable weaknesses even in fully updated, production-grade systems.
Heading into day two, the team from DEVCORE maintained a strong lead, largely driven by Orange Tsai’s impressive achievement on day one, where four chained logic flaws enabled a sandbox escape in Microsoft Edge.
Among the highlights of day two, Microsoft Exchange and Windows 11 were both compromised. Researcher Siyeon Wi showcased a Windows 11 privilege escalation vulnerability tied to an integer overflow issue, earning $7,500. The repeated success of attacks against fully patched Windows 11 systems over the course of the event emphasized lingering security gaps in one of the most widely used operating systems.
In another successful demonstration, Ben Koo from Team DDOS exploited a use-after-free vulnerability in Red Hat Enterprise Linux for Workstations, achieving privilege escalation and earning $10,000.
Artificial intelligence-related targets continued to draw attention. Researcher Byung Young Yi attempted to exploit LiteLLM, but the finding overlapped with an already demonstrated vulnerability, resulting in a duplicate submission. Despite this, Yi was awarded $17,750 and received partial credit toward the Master of Pwn ranking, reflecting the intense focus researchers placed on this AI-focused component.
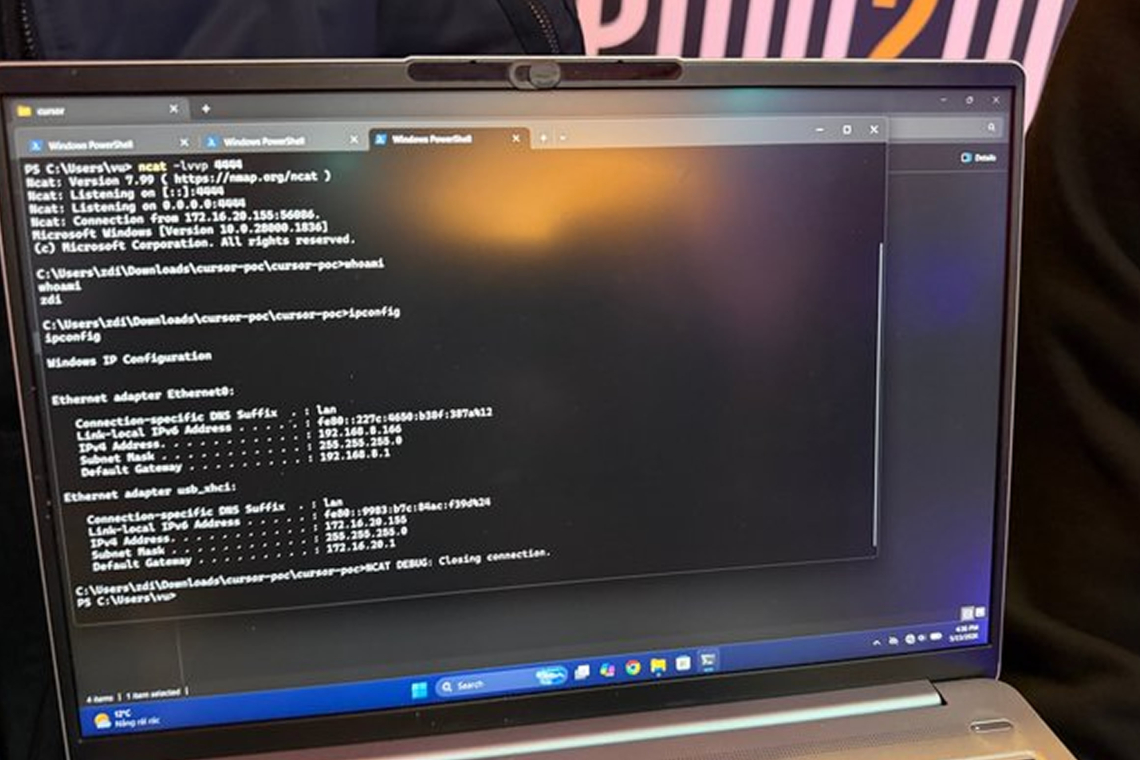
Security firm Compass Security also successfully demonstrated an exploit against the AI-powered code editor Cursor, earning $15,000. This, along with prior successful attacks on OpenAI Codex, highlights the growing security concerns surrounding AI-assisted development tools and supporting infrastructure.
Not every attempt succeeded. Teams targeting Safari and Microsoft SharePoint were unable to complete their exploits within the allotted time. Even with thorough preparation, the strict time constraints and live demonstration format proved challenging, particularly when dealing with fully patched environments.
DEVCORE remains at the top of the leaderboard with 40.5 points and total earnings of $405,000. However, with one day remaining and high-value targets such as Firefox and additional AI systems still in scope, the rankings could shift dramatically with a single successful exploit.
Over the first two days, participants collectively identified 39 zero-day vulnerabilities across a wide range of technologies, including operating systems, enterprise software, and AI platforms. All targets were fully updated, further highlighting the sophistication and persistence of modern vulnerability research.
As per Pwn2Own rules, affected vendors now have a 90-day window to address and remediate the disclosed flaws before technical details are made public, transforming live exploit demonstrations into coordinated vulnerability disclosure.
For context, day one of the competition featured 22 successful entries and 24 zero-days, with total rewards reaching $523,000.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.