Remote Monitoring and Management (RMM) tools are foundational to modern IT operations. Security and IT teams rely on them daily for patching, troubleshooting, automation, and managing entire infrastructures remotely.
They offer efficiency, centralized control, and flexibility capabilities every IT department depends on. But these same strengths have increasingly made RMM platforms attractive targets for cybercriminals. What once gave IT teams an edge is now one of the most exploited entry points in today’s threat landscape.
The scope of the problem continues to grow. According to the Huntress 2026 Cyber Threat Report, RMM abuse surged 277% in 2025. Attackers are shifting away from traditional malware delivery and firewall‑bypass methods and are instead turning trusted remote management tools against the organizations that rely on them.
By leveraging legitimate, already‑approved RMM applications, adversaries gain hands-on-keyboard access without triggering immediate suspicion. Huntress analysts found that a major driver of this trend is that valid RMM binaries appear benign to most security products.
Security tools can recognize malware signatures, ransomware behavior, or remote access trojans but a legitimate RMM executable looks like normal IT activity, allowing an attacker to blend in.
Notably, Huntress reported that over half of suspicious Atera RMM incidents were linked directly to ransomware deployments.
Once an RMM tool is compromised, the attacker inherits its full functionality: running commands, automating tasks, moving laterally, and deploying ransomware. The 2026 Huntress report found that when tools such as Atera or RustDesk are weaponized, ransomware impact can begin within one to two hours. During that time, the attacker masquerades as a legitimate admin, quietly disabling defenses and expanding access.
Initial access almost always starts with human error. Phishing and social engineering remain the primary delivery mechanisms, often disguised as e‑signature requests, invoices, or shared documents. A single click can install an RMM agent that connects directly to the attacker, immediately establishing interactive control.
How Attackers Abuse RMM Access
Once inside, adversaries take advantage of the trust placed in authorized tools. Many IT teams assume that if a tool is on the allow list, any activity from it is safe a dangerous assumption that attackers exploit.
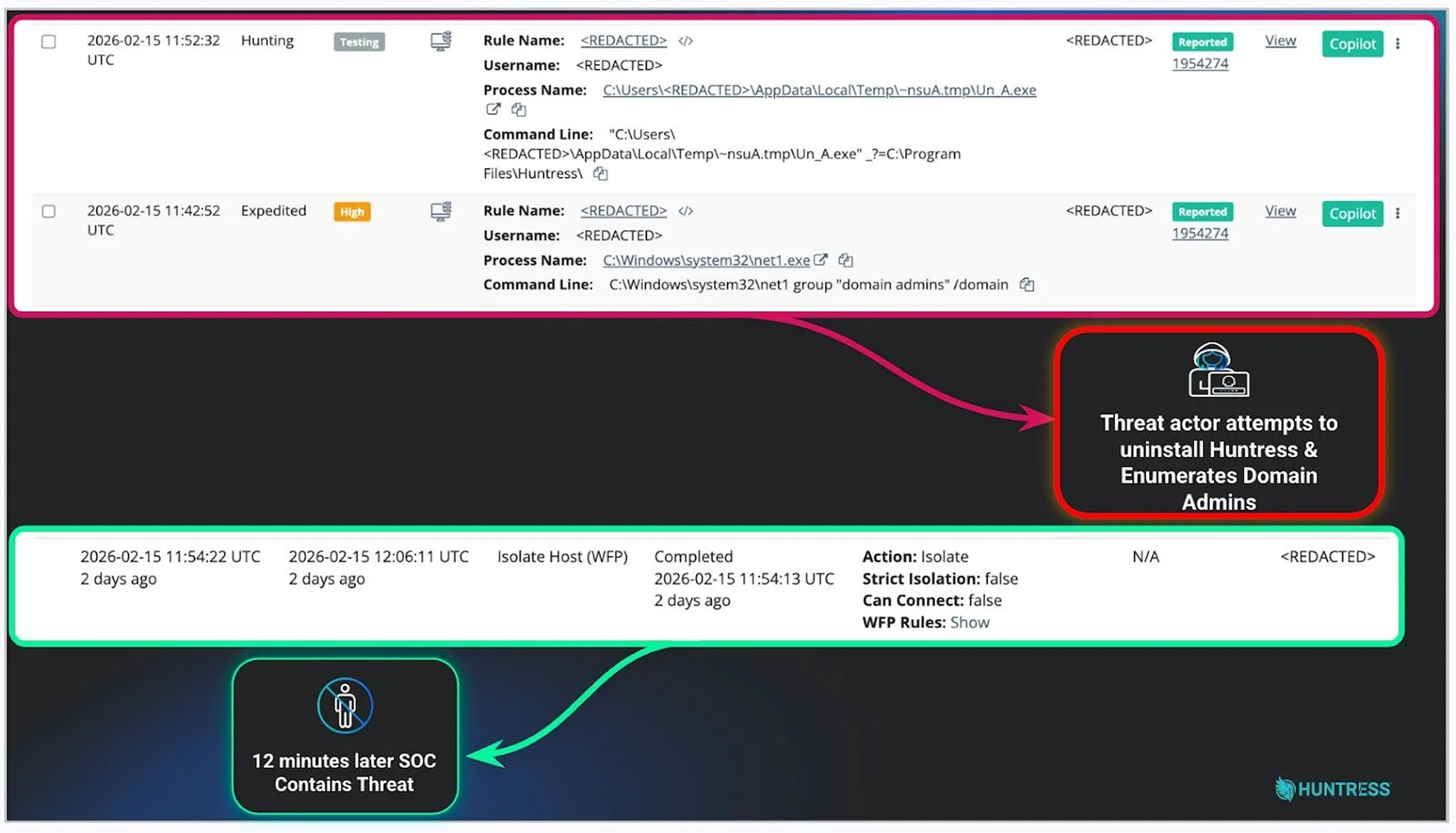
In one investigation handled by the Huntress SOC, a threat actor used stolen RMM credentials to access a managed service provider’s environment, run discovery commands, and attempt to disable the Huntress agent. Because the credentials belonged to an IT support technician, the attacker could have compromised every client managed by that MSP if the intrusion had not been contained quickly.
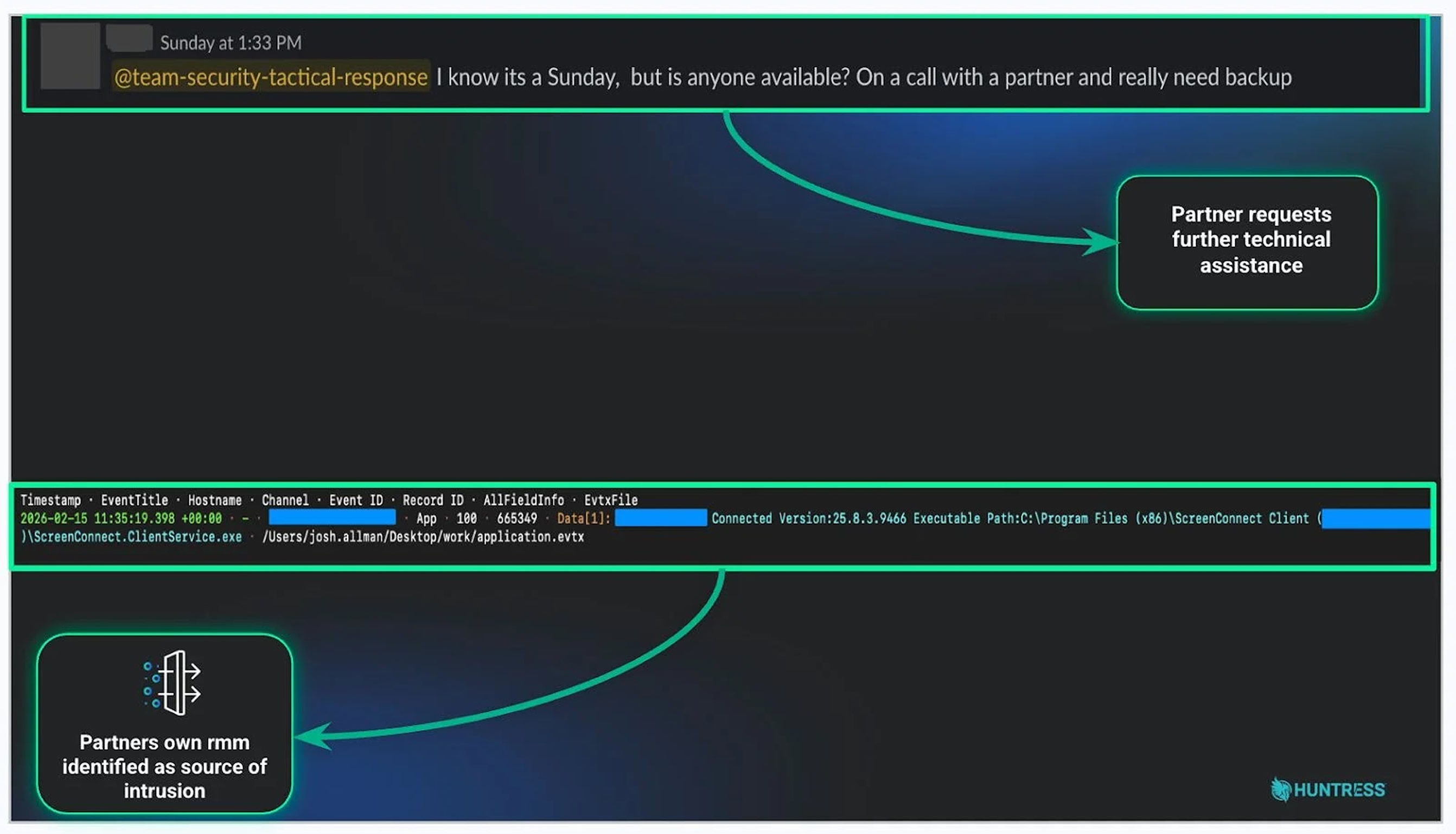
In supply-chain environments, a single compromised MSP account can cascade into dozens of victim organizations in minutes.
Strengthening Defense Against RMM Abuse
Security teams must move beyond trusting tool presence and instead verify tool behavior. This includes knowing:
- Which users typically connect
- When they connect
- From which IPs or regions
Any activity outside these patterns deserves immediate investigation, even if it comes from a well‑known tool.
Organizations should maintain a detailed inventory of all approved RMM solutions including executable hashes and sanctioned connection points so that unknown binaries or suspicious connections generate alerts.
Regular security awareness training remains essential. Teaching employees to recognize phishing attempts significantly reduces the likelihood of malicious RMM agents being installed in the first place.
Finally, building a culture in which users feel comfortable reporting suspicious behavior can narrow the time between compromise and detection often more effectively than any single security technology.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.



