Cybersecurity analysts have identified a newly discovered malware strain known as Speagle, which abuses the features and backend infrastructure of a legitimate software product called Cobra DocGuard.
According to a report released today by researchers from Symantec and Carbon Black, Speagle operates covertly by collecting sensitive data from infected systems and sending it to a Cobra DocGuard server that has already been taken over by the attackers. By routing stolen information through a trusted client‑server communication channel, the malware disguises its exfiltration activity as normal, legitimate traffic.
Cobra DocGuard is a document protection and encryption solution developed by EsafeNet. Its misuse in real-world cyberattacks has been documented on two prior occasions. In January 2023, ESET disclosed an incident involving a gambling firm in Hong Kong that was compromised in September 2022 through a malicious software update delivered via Cobra DocGuard.
Several months later, in August, Symantec reported on a previously unknown threat group dubbed Carderbee, which leveraged a trojanized version of Cobra DocGuard to deploy PlugX, a well-known backdoor frequently associated with Chinese threat actors such as Mustang Panda. Those campaigns targeted organizations across Hong Kong and other parts of Asia.
At present, Speagle has not been definitively linked to any known threat actor. What sets it apart, however, is its narrow targeting logic: the malware only activates data collection and exfiltration routines on systems where Cobra DocGuard is installed. This activity cluster is being monitored under the name Runningcrab.
“This behavior suggests intentional targeting, potentially for intelligence gathering or industrial espionage,” researchers from Broadcom’s threat hunting teams noted. “Current assessments indicate the operation may be tied either to a state-sponsored entity or to a specialized private contractor offering offensive services.”
The initial infection vector remains unclear, though investigators suspect a supply chain compromise, consistent with the earlier incidents involving Cobra DocGuard.
The role of the legitimate security software and its infrastructure is particularly significant. Speagle not only relies on a compromised Cobra DocGuard server for command-and-control (C2) and data exfiltration, but it also uses an associated driver to remove itself from infected machines, helping it evade detection.
Once executed, the 32-bit .NET malware first verifies the presence of Cobra DocGuard by checking its installation directory. It then proceeds to collect and transmit data in stages, including system information and files stored in targeted directories such as those containing web browser history and autofill credentials.
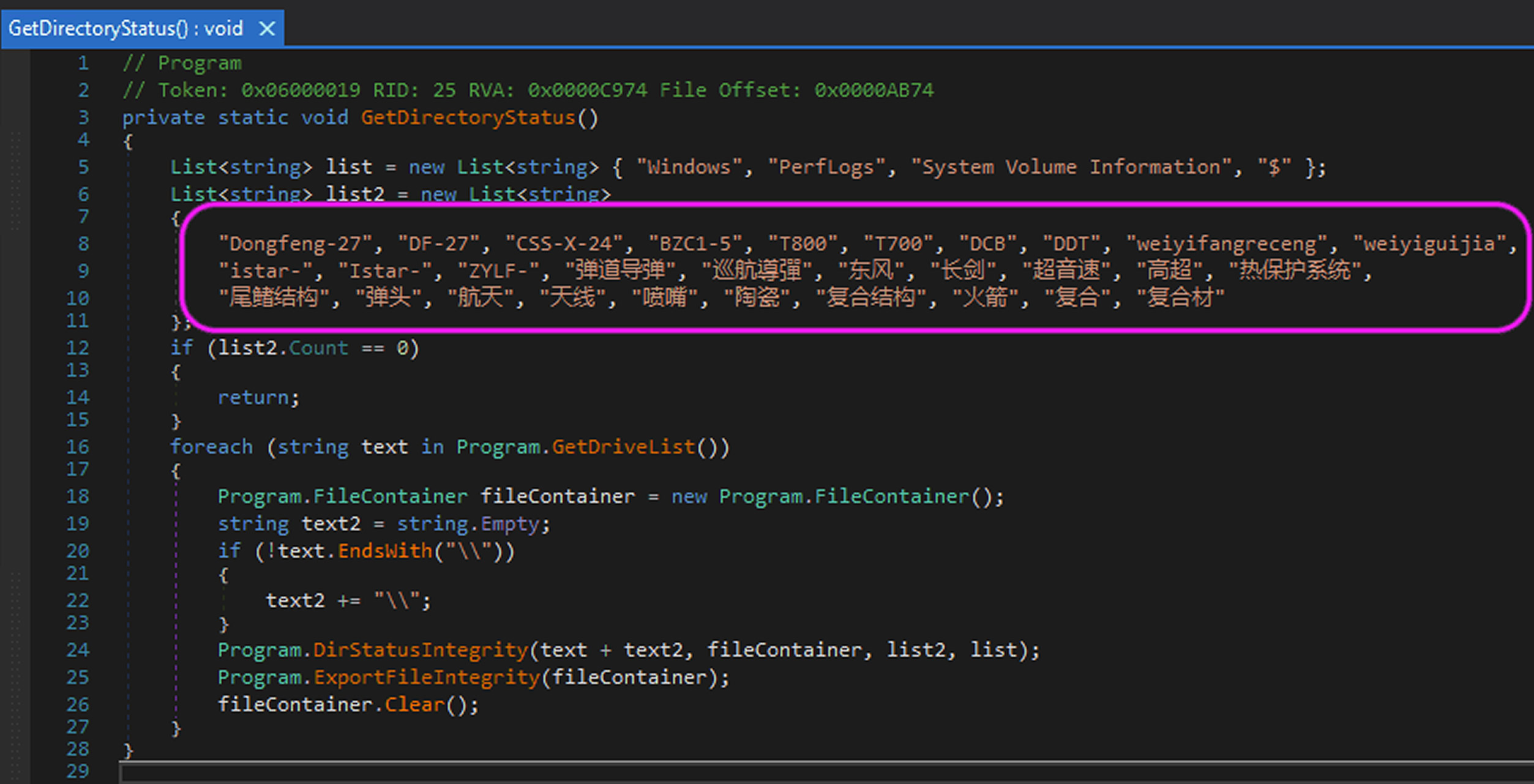
Additionally, one observed variant of Speagle includes expanded capabilities that allow operators to selectively enable or disable specific data collection modules. That same variant also searches for files referencing Chinese ballistic missile systems, including Dongfeng‑27 (DF‑27).
“Speagle represents a sophisticated and parasitic threat,” researchers concluded. “By exploiting Cobra DocGuard’s client software to conceal malicious behavior and its infrastructure to obscure exfiltration traffic, the malware demonstrates a high level of operational awareness. Its developer likely drew lessons from earlier supply chain abuses of the platform, choosing it both for its apparent weaknesses and its widespread deployment among high-value targets.”
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.



