AstraZeneca, the Swedish‑British pharmaceutical giant, has surfaced on a hacker‑operated website, where attackers allege they have compromised the company’s internal systems. The threat actors claim access to AstraZeneca’s source code, cloud infrastructure, and multiple sensitive credentials. The company’s name appeared on a blog associated with Lapsus$, a group known for publicizing high‑profile victims.
According to the attackers, they extracted several gigabytes of internal data, including what they describe as complete source code repositories and employee information. Portions of the allegedly stolen data have also been advertised on a dark‑web leak forum.
Headquartered in Cambridge, AstraZeneca is one of the world’s largest pharmaceutical companies, reporting more than $58.7 billion in revenue in 2025 and employing approximately 90,000 people globally.
The company has been contacted for comment, and updates will be provided if a response is received.
What data do the attackers claim to have accessed?
Based on statements posted by Lapsus$ across at least two platforms, the attackers allege they gained access to multiple internal systems and databases, exposing:
- Complete source code repositories
- Employee databases
- GitHub Enterprise user information
- Internal API credentials
- AWS keys and service accounts
- MongoDB data
- MySQL credentials
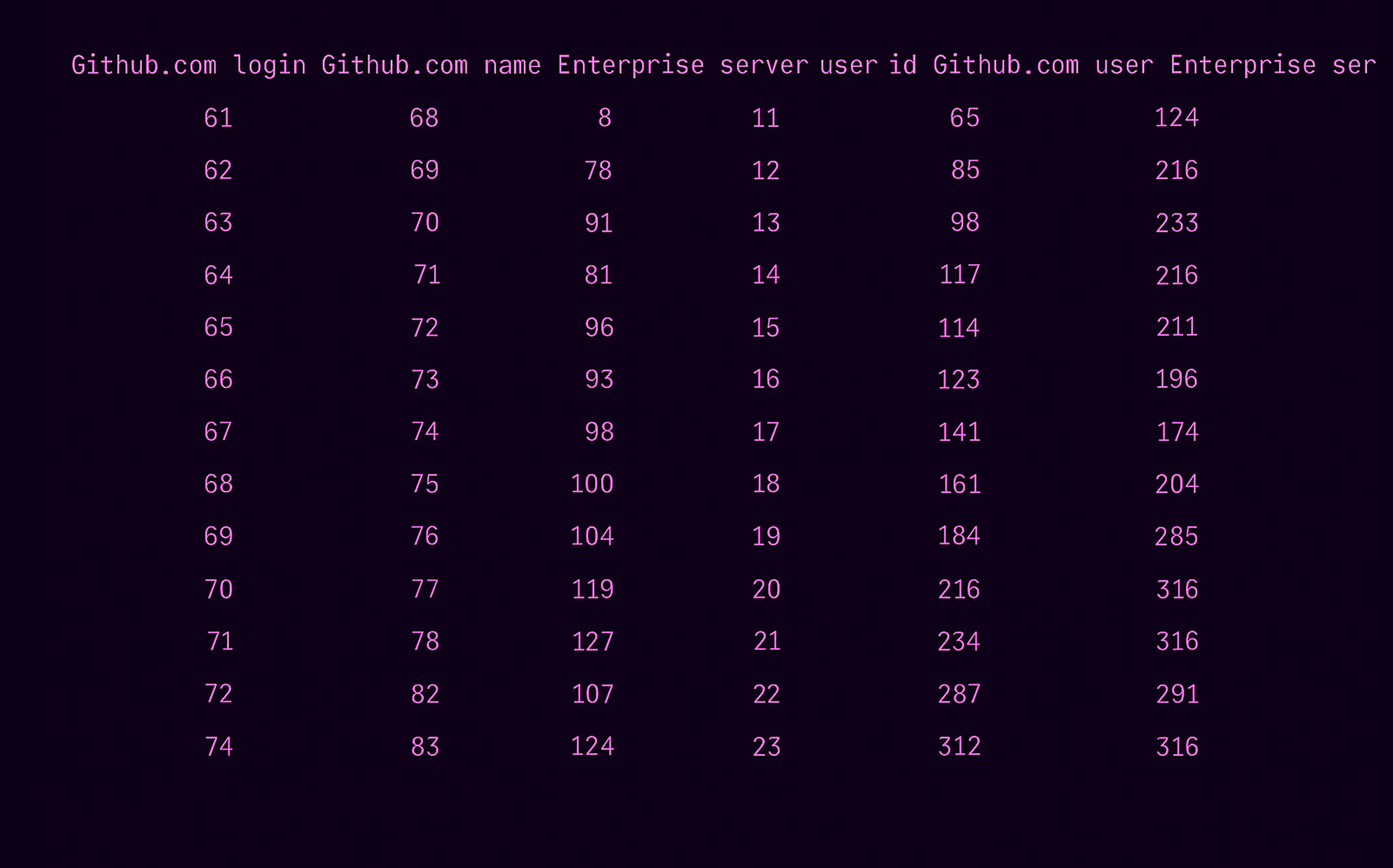
The Cybernews research team reviewed sample data shared by the attackers on their Telegram channel and found that some of the claims appear credible. One dataset reportedly contains GitHub‑related information tied to AstraZeneca’s internal development teams, including:
- GitHub workspace identifiers
- Employee roles within development teams
- Links to individual GitHub profiles
- Full names
- Corporate email addresses
Another dataset allegedly includes employee records associated with various AstraZeneca‑linked clinical research organizations, revealing:
- Full names
- Work email addresses
- User identifiers
- Company affiliations
A third data sample shared by the attackers appears to show a directory tree structure of internal software source code.
Potential risks stemming from the alleged breach
If the attackers’ claims are verified, AstraZeneca could face significant security and business risks. Access to proprietary source code could enable competitors or malicious actors to identify exploitable vulnerabilities deep within the company’s systems.
Given the scale of AstraZeneca’s research and development efforts—often spanning years and involving highly sensitive intellectual property—the exposure of internal code and credentials could have serious financial and strategic consequences.
“If the attackers truly possess the company’s source code, it could be analyzed for hard‑coded secrets or security weaknesses,” researchers noted. “Such findings could ultimately lead to further system compromise or intellectual property theft.”
In addition, employees whose information may have been exposed could become targets of highly tailored phishing and social engineering attacks. Given Lapsus$’s past collaboration with groups such as ShinyHunters, individuals with elevated access privileges could face heightened risk.
Who is Lapsus$?
Lapsus$ rose to prominence in 2022 after a string of high‑profile breaches affecting companies such as Okta, Nvidia, Samsung, and T‑Mobile. Several members of the group were later arrested in the United Kingdom, though activity linked to the name has continued.
Most recently, the group claimed responsibility for a breach involving Adidas’ Extranet, alleging access to user credentials and internal technical data. Adidas, however, stated that there was no evidence its core IT systems, e‑commerce platforms, or consumer data were impacted.
In a report published late last year, Resecurity identified Lapsus$, Scattered Spider, and ShinyHunters as three of the most prominent English‑speaking cybercrime groups currently operating, known for their aggressive tactics and focus on high‑value corporate targets.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.