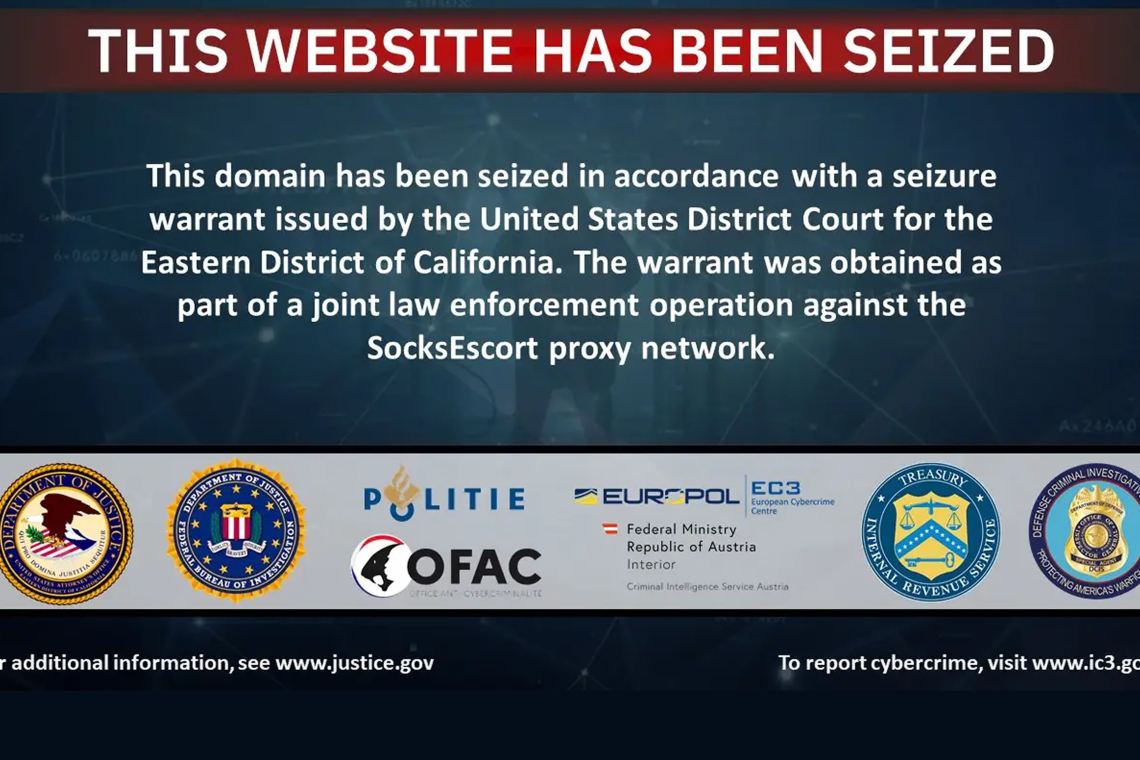
Authorities Dismantle SocksEscort Residential Proxy Network
Law enforcement agencies have taken down a large-scale cybercrime operation known as SocksEscort, a covert residential proxy service that hijacked roughly 369,000 home routers and connected devices worldwide. The platform allowed cybercriminals to disguise malicious activity behind legitimate residential IP addresses often without the knowledge of the affected users.
SocksEscort openly promoted itself as a residential proxy provider, selling access to everyday household internet connections. Customers were offered “static residential IPs with unlimited bandwidth,” with pricing tiers ranging from $15 per month for 30 residential IPs to $200 per month for 5,000 proxies.
International Law Enforcement Operation
The U.S. Department of Justice (DoJ) announced that authorities from eight countries worked together to dismantle the operation. According to officials, the service was used to compromise thousands of residential routers globally and facilitate large-scale fraud.
As part of the takedown:
- 34 domains and 23 servers were seized across seven countries
- $3.5 million in cryptocurrency was frozen by U.S. authorities
- Infected devices were disconnected from the proxy infrastructure
Europol confirmed that the compromised modems and routers providing proxy access have now been removed from the network.
How the Network Operated
The SocksEscort infrastructure primarily routed malicious traffic through compromised Wi‑Fi routers. The operators relied on AVrecon malware to infect approximately 1,200 device models, targeting older or unpatched hardware.
Affected manufacturers included:
- Cisco
- D‑Link
- Hikvision
- MikroTik
- Netgear
- TP‑Link
- Zyxel
Investigators estimate that around 369,000 devices have been compromised and monetized by SocksEscort since 2020.
Criminal Use and Financial Impact
According to the DoJ, cybercriminals who purchased access to SocksEscort used the service to mask their real IP addresses and locations, enabling a range of fraud schemes. These included:
- Bank and cryptocurrency account takeovers
- Fraudulent unemployment insurance claims
- Identity‑based financial crimes
Authorities reported millions of dollars in losses, citing examples such as:
- A New York cryptocurrency exchange customer defrauded of $1 million
- A Pennsylvania manufacturing firm that lost $700,000
- U.S. service members with MILITARY STAR cards defrauded of $100,000
Overall, SocksEscort is believed to have generated more than €5 million ($5.72 million) in revenue from proxy service customers, with payments accepted exclusively via cryptocurrency.
Europol Executive Director Catherine De Bolle emphasized that proxy services like SocksEscort provide criminals with critical anonymity, enabling attacks, illegal content distribution, and evasion of detection. She noted that dismantling the infrastructure significantly disrupts cybercrime on a global scale.
Additional Criminal Activity
Beyond financial fraud, the botnet of infected devices was also leveraged to:
- Support ransomware operations
- Launch distributed denial‑of‑service (DDoS) attacks
- Distribute child sexual abuse material (CSAM)
- Facilitate other forms of cybercrime
How to Protect Your Router
Authorities warn that attackers specifically targeted end‑of‑life and unpatched routers, especially those exposed directly to the internet. AVrecon malware primarily infects routers and IoT devices lacking antivirus protection, endpoint detection, or similar safeguards.
In a flash advisory, the FBI explained that threat actors exploit known vulnerabilities to install malware, seize control of devices, and resell access as residential proxies.
The FBI recommends:
- Keeping operating systems, firmware, and software fully updated
- Replacing devices that are no longer supported by manufacturers
- Disabling remote administration features
- Restricting exposed services using firewall rules or access control lists
- Monitoring logs and network traffic for suspicious activity
Commonly Abused Devices
The FBI identified several device models frequently exploited by SocksEscort, including:
- D‑Link routers: DIR‑818LW, DIR‑850L, DIR‑860L
- Hikvision IP camera models
- Netgear routers: DGN2200v4, R7000
- TP‑Link routers: Archer C20, TL‑WR840N, TL‑WR849N, WR841N
- Multiple Zyxel routers, including VMG3925‑B10A and VMG3925‑B10C
Many of these devices are commonly supplied by internet service providers, increasing their exposure.
Why Residential Proxies Remain a Threat
Despite the shutdown of SocksEscort, vulnerable routers continue to be attractive targets for other botnets. The FBI stresses that many people are unaware their internet connections can be exploited without consent.
Residential proxy networks obtain IP addresses either:
- With the device owner’s consent, or
- Without consent, leaving the owner completely unaware
Malware infections are not the only path to compromise. The FBI warns that many devices become part of residential proxy networks after users:
- Install free VPNs with hidden proxy enrollment terms
- Download pirated software bundled with malware
- Purchase low‑cost, off‑brand devices preloaded with malicious code
Some consumer electronics such as streaming devices, digital projectors, smart picture frames, vehicle infotainment systems, and other IoT products may arrive infected or become compromised while downloading required applications.
Proxy services also lure users with apps that promise payment for unused internet bandwidth.
The FBI advises consumers to avoid devices or services advertising free access to sports, movies, or TV content, to stay away from pirated software, and to exercise caution when installing free VPN applications.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.