A high‑severity vulnerability in the TrueConf video conferencing client has been actively exploited as a zero‑day in a targeted campaign against government organizations in Southeast Asia, known as TrueChaos.
Tracked as CVE‑2026‑3502 (CVSS score: 7.8), the flaw stems from insufficient integrity verification during the application’s update process. This weakness allows attackers to deliver a maliciously modified update package, ultimately enabling arbitrary code execution on vulnerable systems. The issue has been addressed in the TrueConf Windows client version 8.5.3, released earlier this month.
According to a report published by Check Point, the vulnerability arises from the misuse of TrueConf’s updater validation mechanism. An attacker who gains control of an on‑premises TrueConf server can distribute and execute malicious files across all connected client endpoints without triggering integrity checks.
In practical terms, adversaries are able to replace legitimate update packages with poisoned versions, which are then automatically downloaded and installed by the TrueConf client due to a lack of proper verification to confirm the update’s authenticity.
The TrueChaos campaign has weaponized this update mechanism to likely deploy the Havoc open‑source command‑and‑control (C2) framework across compromised systems. Check Point attributes the activity with moderate confidence to a threat actor with links to China.
The exploitation activity was first observed in early 2026, when attackers abused the trust relationship between the TrueConf client and its update server to push a rogue installer. The malicious update leveraged DLL side‑loading techniques to launch a backdoor component.
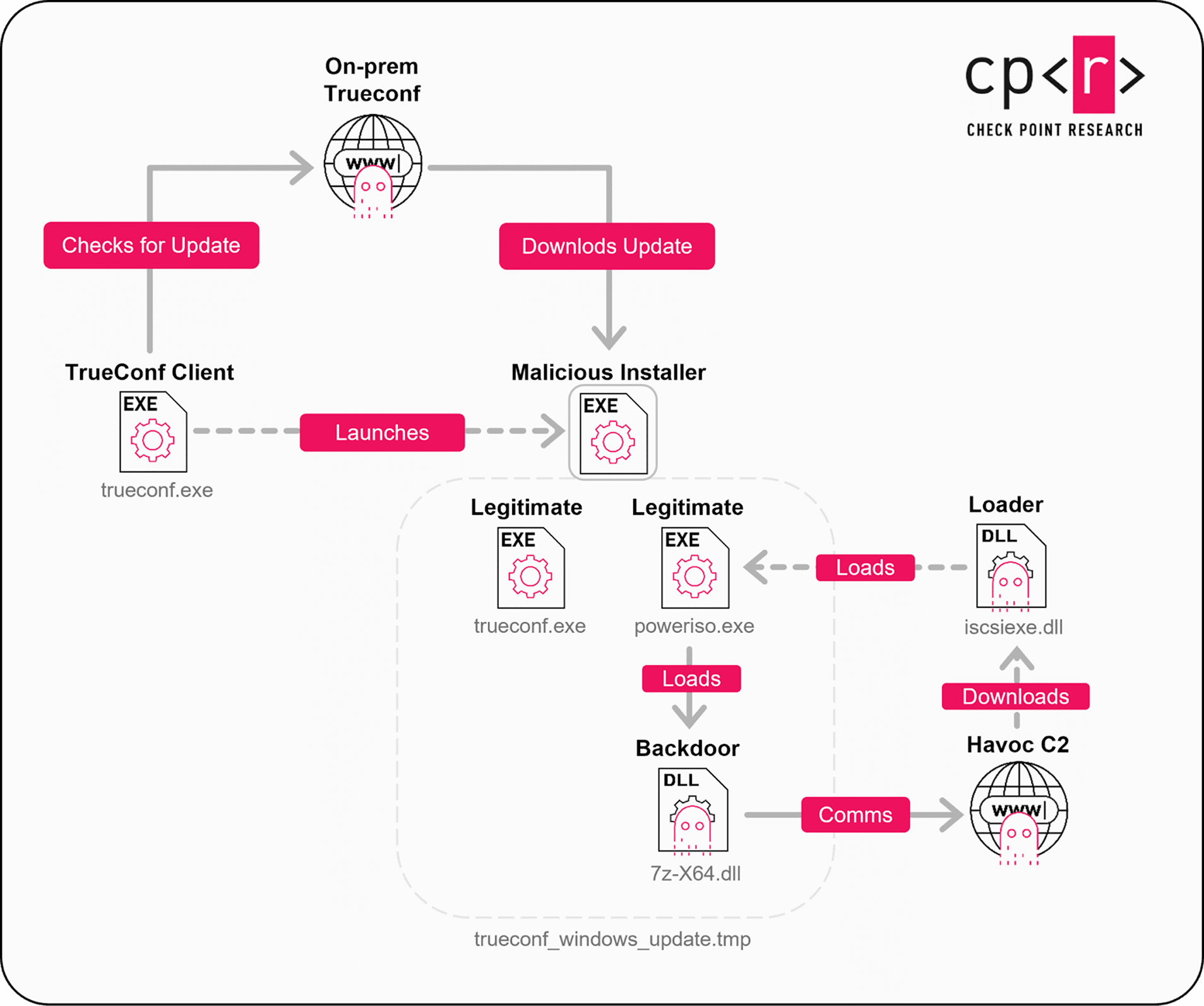
One observed implant, 7z‑x64.dll, performed interactive, hands‑on‑keyboard actions including system reconnaissance, persistence setup, and staged payload retrieval. Additional payloads—such as iscsiexe.dll were downloaded from an attacker‑controlled FTP server (47.237.15[.]197). The purpose of this module was to execute a legitimate‑looking binary (poweriso.exe) used to sideload the backdoor.
While the precise final‑stage malware deployed during the campaign remains unconfirmed, analysts assess with high confidence that the ultimate objective was to install the Havoc implant.
Evidence linking the TrueChaos campaign to Chinese‑aligned threat actors includes the use of DLL side‑loading, reliance on Alibaba Cloud and Tencent infrastructure for command‑and‑control, and overlap with activity involving ShadowPad, a sophisticated backdoor frequently associated with China‑linked cyber operations. The same victim organization was targeted by ShadowPad during the same time period.
Additionally, Havoc usage has previously been tied to another Chinese‑linked group, Amaranth‑Dragon, which conducted intrusions against government and law enforcement targets across Southeast Asia in 2025.
As Check Point noted, exploitation of CVE‑2026‑3502 eliminated the need for attackers to compromise endpoints individually. Instead, adversaries abused the trusted update channel between a centralized TrueConf server and its clients, effectively transforming the legitimate update process into a malware distribution mechanism spanning multiple connected government networks.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.