A pro‑Ukraine hacktivist collective known as PhantomCore has been linked to an ongoing campaign targeting servers running TrueConf video conferencing software across Russia. Evidence suggests the activity has been underway since September 2025.
The attribution comes from a report released by Positive Technologies, which determined that the attackers leveraged a multi‑step exploit chain combining three separate vulnerabilities to achieve remote command execution against exposed TrueConf Server installations.
According to researchers Daniil Grigoryan and Georgy Khandozhko, the attack is notable because no public exploit code existed for the vulnerability chain. Despite this, PhantomCore independently analyzed the product, reproduced the flaws, and weaponized them at scale. This effort resulted in widespread exploitation across Russian organizations using the platform.
Background on PhantomCore
Also known by several aliases including Fairy Trickster, Head Mare, Rainbow Hyena, and UNG0901 PhantomCore is a politically and financially motivated threat group that emerged in 2022, following the escalation of the Russo‑Ukrainian conflict. The group has built a reputation for conducting disruptive intrusions against Russian entities, frequently stealing sensitive data and interfering with internal operations. In some incidents, PhantomCore has even deployed ransomware derived from leaked source code tied to well‑known families such as Babuk and LockBit.
Positive Technologies previously highlighted the group’s operational maturity, noting that PhantomCore conducts large‑scale campaigns while maintaining a high level of stealth. Its ability to remain undetected for extended periods is attributed to ongoing enhancements to its internally developed toolsets and attack techniques.
Vulnerabilities exploited in TrueConf Server
The attacks focused on a trio of vulnerabilities affecting TrueConf Server, outlined below:
- BDU‑2025‑10114 (CVSS 7.5): An access control weakness allowing unauthenticated requests to reach administrative endpoints under
/admin/*. - BDU‑2025‑10115 (CVSS 7.5): A file disclosure flaw enabling attackers to read arbitrary files from the underlying system.
- BDU‑2025‑10116 (CVSS 9.8): A command injection vulnerability that permits arbitrary operating system command execution.
When chained together, these flaws allow attackers to bypass authentication entirely and gain deep access to the target’s internal network. Although TrueConf issued patches on August 27, 2025, Positive Technologies reported that the first active exploitation attempts were observed around mid‑September 2025, indicating rapid attacker adoption following disclosure.
Post‑compromise activity and lateral movement
Once the TrueConf Server was compromised, PhantomCore used it as an entry point for broader internal compromise. From there, attackers moved laterally through enterprise networks and deployed additional payloads to support reconnaissance, credential theft, and defense evasion. In several cases, tunneling tools were used to establish covert communication channels back to attacker‑controlled infrastructure.
At least one confirmed incident involved the installation of a PHP‑based web shell that enabled file uploads and remote command execution. The attackers also deployed an additional PHP component that acted as a proxy, allowing malicious traffic to masquerade as legitimate server communications.
Tooling observed in the campaign
The campaign made use of a diverse toolkit, blending proprietary malware with publicly available utilities:
- PhantomPxPigeon: A trojanized TrueConf client that provides a reverse shell, enabling command execution, binary deployment, and traffic proxying via the installed web shell.
- PhantomSscp (DLL), MacTunnelRAT (PowerShell), and PhantomProxyLite (PowerShell): Used to establish persistence and maintain access through reverse SSH tunneling.
- ADRecon: Deployed for Active Directory reconnaissance.
- Veeam‑Get‑Creds: A modified script used to extract credentials associated with Veeam Backup & Replication.
- DumpIt and MemProcFS: Leveraged for credential harvesting through memory dumping.
- WinRM and RDP: Used to facilitate lateral movement within compromised networks.
- Velociraptor: Employed for remote access and post‑exploitation operations.
- microsocks, rsocx, and tsocks: Used to build SOCKS‑based proxy infrastructure for command‑and‑control operations.
In select intrusions, attackers also deployed a DLL that created a rogue administrative account named “TrueConf2” on the compromised server to ensure persistent privileged access.
Additional initial access vectors
Beyond exploiting server‑side flaws, PhantomCore has also continued to rely on phishing campaigns to gain initial access. As recently as January and February 2026, the group distributed malicious ZIP and RAR archives containing backdoors capable of executing remote commands and retrieving additional payloads from attacker infrastructure.
Positive Technologies characterized PhantomCore as one of the most aggressive and capable adversaries currently operating against Russian organizations. The group mixes well‑known open‑source tools such as Velociraptor, MemProcFS, Dokan, and DumpIt with custom malware like MacTunnelRAT, PhantomSscp, and PhantomProxyLite. Targets span both government and private‑sector organizations across numerous industries.
The researchers emphasized that PhantomCore actively hunts for weaknesses in locally developed software and invests heavily in exploit development, enabling broad penetration across Russian enterprises.
Broader threat landscape
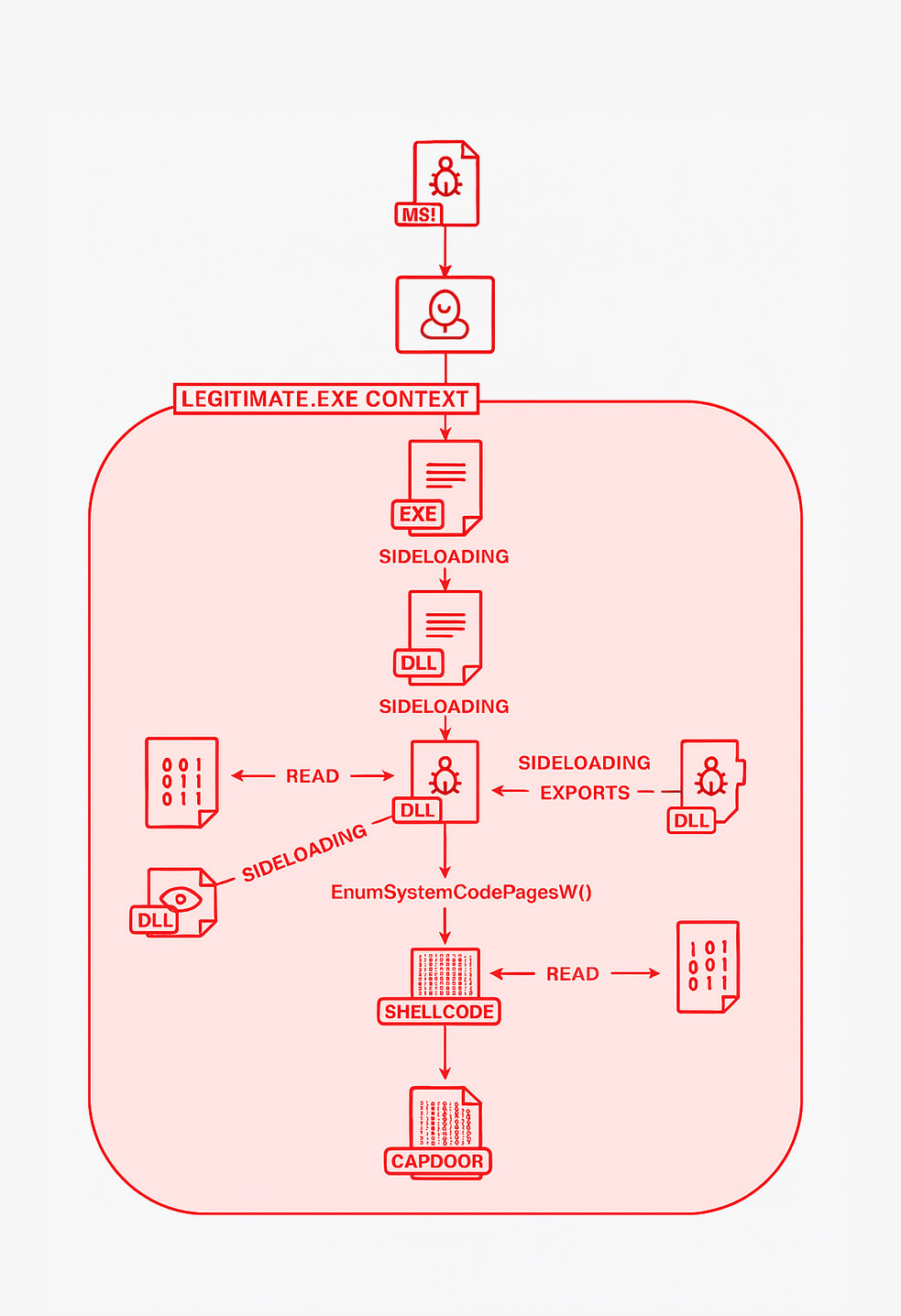
PhantomCore is not the only group conducting campaigns against Russian organizations. In recent months, industries such as manufacturing and aviation have also been targeted by phishing campaigns linked to a financially motivated actor known as CapFIX. This group distributes a backdoor named CapDoor, capable of executing PowerShell commands, loading DLLs and executables, installing MSI packages, and capturing screenshots. CapDoor was initially identified in 2025 and delivered using the ClickFix social engineering technique.
Further analysis of CapFIX activity in October and November 2025 revealed the use of ClickFix to distribute commodity malware families such as AsyncRAT and SectopRAT. While CapFIX initially relied on finance‑themed phishing lures, recent campaigns increasingly impersonate official communications from Russian government agencies.
Several other threat clusters have also been active in the region:
- Geo Likho: Targeting aviation and shipping sectors in Russia and Belarus since mid‑2024 using phishing‑delivered data‑stealing malware, with sporadic spillover cases in Europe and Asia.
- Mythic Likho: Delivering loaders such as HuLoader, Merlin, and ReflectPulse to deploy a Loki backdoor built for Mythic and Havoc frameworks, with links to the ExCobalt group.
- Paper Werewolf (GOFFEE): Distributing EchoGather trojans via Telegram channels and fake Starlink‑related tools, while also harvesting Telegram account credentials.
- Versatile Werewolf (HeartlessSoul): Using fraudulent websites and drone‑themed installers to deploy the Sliver framework and SoullessRAT.
- Eagle Werewolf: A newly observed actor spreading AquilaRAT through compromised drone‑focused Telegram channels using Rust‑based droppers.
According to BI.ZONE, while these groups share overlapping objectives and techniques, there is no clear evidence that they coordinate directly. The firm also noted that Paper Werewolf actively hijacks Telegram accounts for future operations, while Versatile Werewolf incorporates generative AI to accelerate malware development.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.