A newly identified cyber‑espionage operation is actively targeting Chinese‑speaking users through a carefully crafted infection chain that leverages a maliciously modified version of the popular SumatraPDF document reader. The campaign ultimately results in the deployment of the AdaptixC2 Beacon post‑exploitation framework and enables threat actors to establish persistent remote access by abusing Microsoft Visual Studio Code (VS Code) tunneling functionality.
The activity was uncovered in March by Zscaler ThreatLabz, which has attributed the campaign with high confidence to Tropic Trooper a well‑established advanced persistent threat (APT) group also tracked under the aliases APT23, Earth Centaur, KeyBoy, and Pirate Panda. Tropic Trooper has a long operational history dating back to at least 2011 and is widely known for conducting espionage operations against government, military, and related organizations across Taiwan, Hong Kong, and the Philippines.
According to the research, the attackers engineered a customized AdaptixC2 Beacon listener and adopted GitHub as a covert command‑and‑control (C2) channel, blending malicious traffic with legitimate developer activity to evade detection. Security researcher Yin Hong Chang highlighted that the use of GitHub infrastructure for C2 operations represents a deliberate effort to masquerade as legitimate traffic while managing compromised hosts.
The campaign primarily targets Chinese‑speaking populations in Taiwan, with additional victims identified in South Korea and Japan. Infection begins when victims are socially engineered into opening a ZIP archive that contains military‑themed decoy documents. These lures are designed to appear credible and relevant to the target audience, increasing the likelihood that the archive will be decompressed and its contents executed.
Embedded within the archive is a trojanized copy of the SumatraPDF executable. Once launched, the modified application behaves as expected from the user’s perspective by displaying a benign PDF document, thereby maintaining the illusion of legitimacy. Behind the scenes, however, the executable simultaneously contacts a remote staging server to retrieve encrypted shellcode, which is then used to initiate the AdaptixC2 Beacon payload.
At the core of this infection process is a loader known as TOSHIS, a lightly altered derivative of the Xiangoop malware family previously linked to Tropic Trooper. This loader has a history of being used by the group to fetch and deploy secondary payloads, including Cobalt Strike Beacons and the Merlin agent associated with the Mythic command‑and‑control framework. In this campaign, TOSHIS serves as the primary orchestrator of the multi‑stage attack chain.
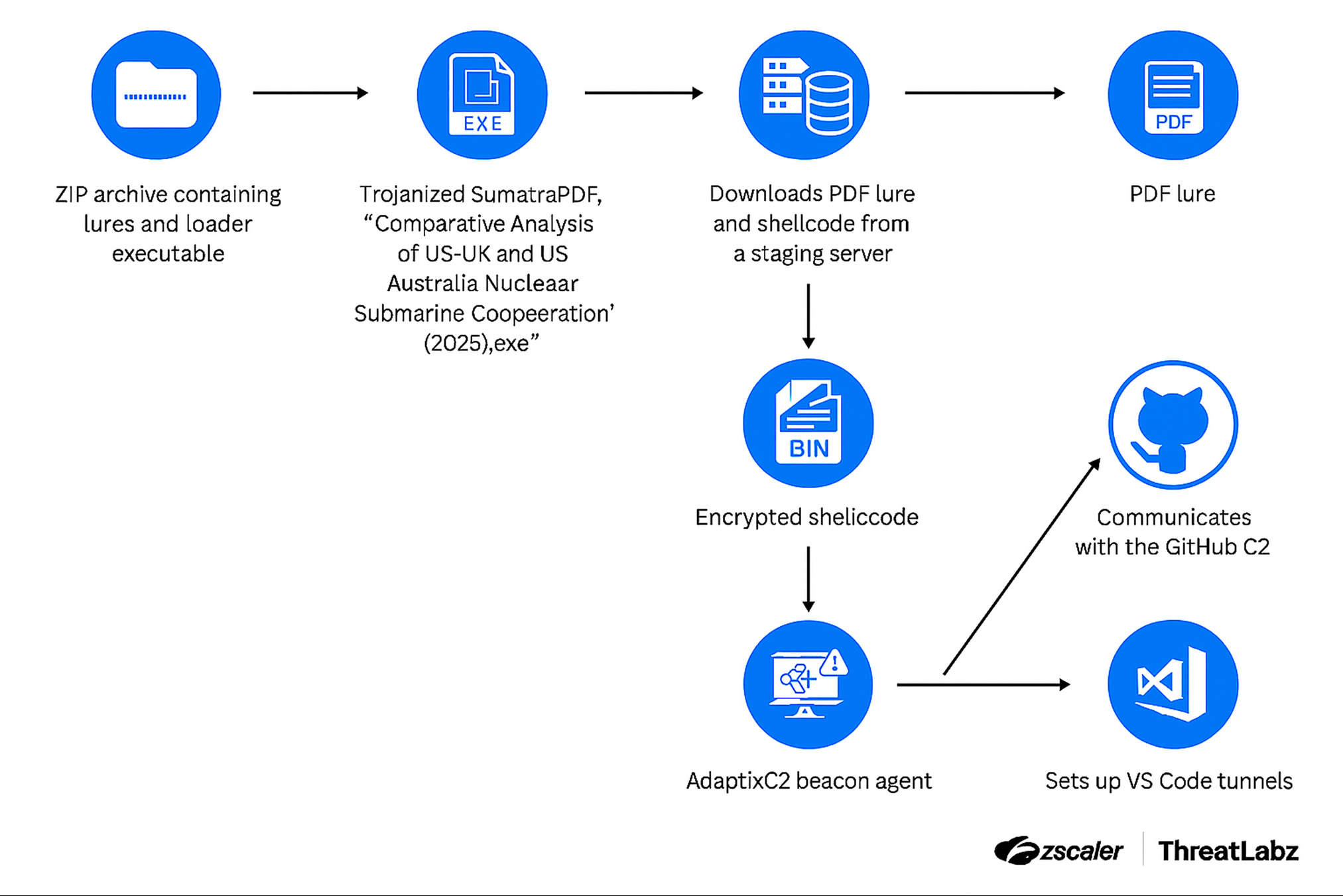
Once executed, the loader drops the decoy document to distract the victim while covertly installing the AdaptixC2 Beacon in the background. The Beacon establishes persistent communication with attacker‑controlled GitHub repositories, periodically beaconing outbound to request instructions and receive tasking commands. These commands allow the attackers to execute arbitrary actions on the compromised host, enabling reconnaissance, lateral movement, and data exfiltration.
Progression to the next stage of the intrusion is conditional. Only when a victim system is assessed as being of high strategic value do the attackers escalate their activity. At this point, they deploy Microsoft Visual Studio Code and configure VS Code tunneling features to create a persistent, interactive remote access channel. This approach allows the attackers to maintain long‑term control over the system while leveraging a legitimate developer tool to minimize suspicion and bypass traditional security controls.
In certain cases, researchers observed the installation of additional trojanized software on select systems. These alternative compromised applications appear to be used as camouflage, further obscuring malicious behavior and blending it into the normal software landscape of the victim environment.
Further analysis revealed that the staging infrastructure used in the campaign specifically the server at 158.247.193[.]100 has historically hosted several known malicious tools associated with Tropic Trooper. These include Cobalt Strike Beacon as well as a proprietary backdoor known as EntryShell, both of which have featured prominently in the group’s previous operations.
Zscaler noted that the campaign reflects continuity with earlier Tropic Trooper operations, such as the TAOTH campaign, in which publicly available post‑exploitation frameworks were favored as payloads. While prior intrusions relied heavily on Cobalt Strike Beacon and the Merlin agent, the threat actor has now transitioned to using AdaptixC2, signaling an evolution in tooling while maintaining consistent tradecraft and targeting methodology.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.