China‑based threat actor Storm‑1175 conducts rapid, financially motivated ransomware operations by exploiting newly disclosed software vulnerabilities and swiftly deploying Medusa ransomware. The group’s strategy relies on attacking organizations before patches are applied, allowing it to move quickly from initial compromise to data theft and encryption sometimes in less than 24 hours.
Storm‑1175 primarily targets internet‑exposed systems and focuses on sectors such as healthcare, education, finance, and professional services, with confirmed victims across the United States, United Kingdom, and Australia. Once access is gained, the actors progress rapidly through the attack lifecycle, chaining exploits, establishing persistence, moving laterally, stealing credentials, and deliberately weakening security controls to maintain momentum. Their emphasis on speed and unpatched environments makes them particularly dangerous and effective.
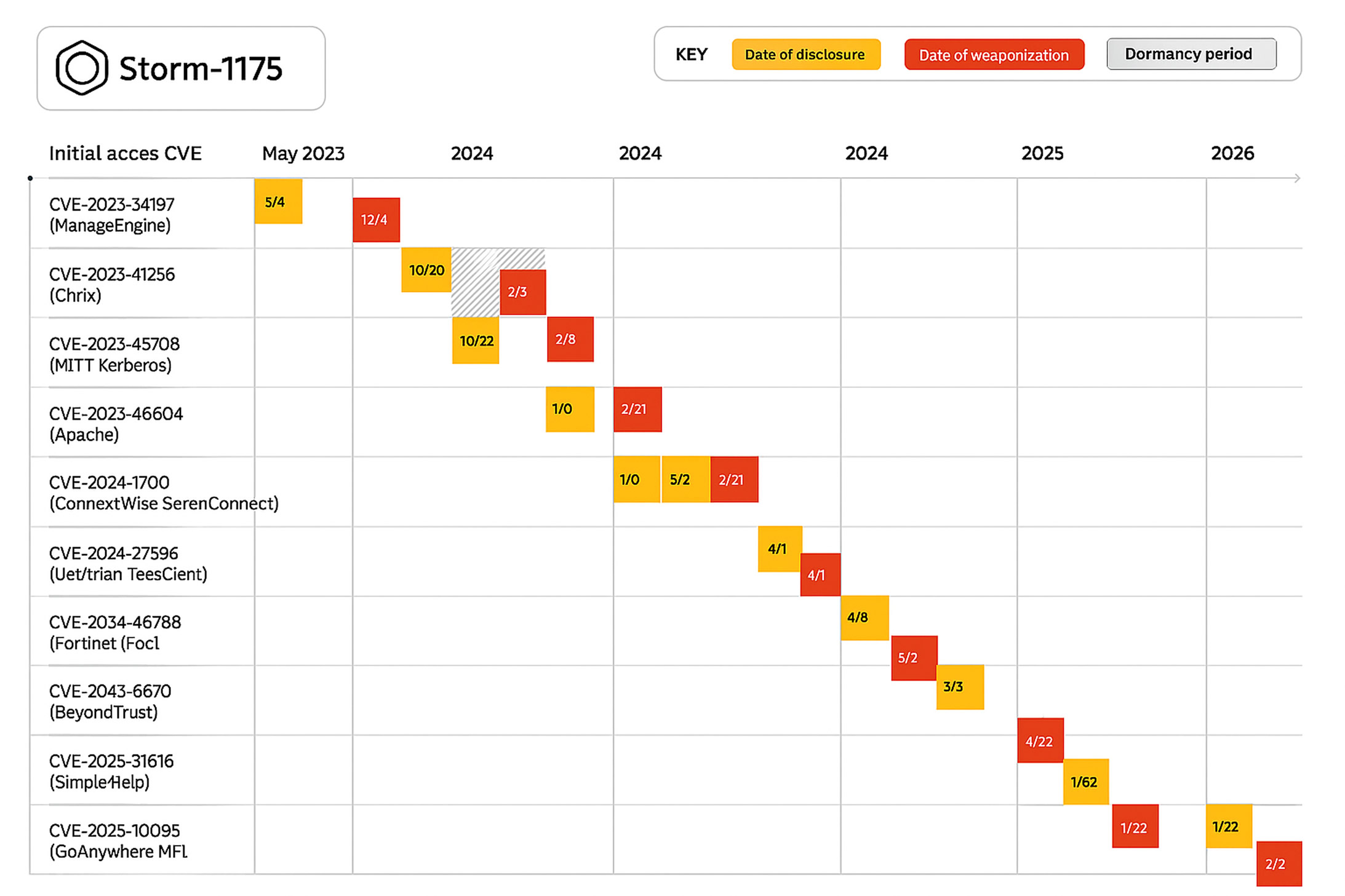
According to Microsoft Threat Intelligence, Storm‑1175 consistently exploits newly revealed vulnerabilities in web‑facing applications to obtain initial access. Since 2023, the group has targeted a wide range of platforms, including Microsoft Exchange, Ivanti, ConnectWise, JetBrains, and others, often weaponizing flaws within days or even hours of public disclosure.
“Storm‑1175 rapidly weaponizes recently disclosed vulnerabilities to obtain initial access,” Microsoft noted in its report. “Since 2023, Microsoft Threat Intelligence has observed exploitation of more than 16 vulnerabilities,” including:
- CVE‑2026‑1731 (BeyondTrust)
- CVE‑2023‑21529 (Microsoft Exchange)
- CVE‑2023‑27351 and CVE‑2023‑27350 (PaperCut)
- CVE‑2023‑46805 and CVE‑2024‑21887 (Ivanti Connect Secure and Policy Secure)
- CVE‑2024‑1709 and CVE‑2024‑1708 (ConnectWise ScreenConnect)
- CVE‑2024‑27198 and CVE‑2024‑27199 (JetBrains TeamCity)
- CVE‑2024‑57726, CVE‑2024‑57727, and CVE‑2024‑57728 (SimpleHelp)
- CVE‑2025‑31161 (CrushFTP)
- CVE‑2025‑10035 (GoAnywhere MFT)
- CVE‑2025‑52691 and CVE‑2026‑23760 (SmarterMail)
The group frequently combines multiple vulnerabilities to achieve deeper levels of access, such as escalating from initial entry to remote code execution. Storm‑1175 has also demonstrated the ability to operate across both Windows and Linux environments and, in some instances, has exploited zero‑day vulnerabilities ahead of public disclosure highlighting its advanced operational maturity.
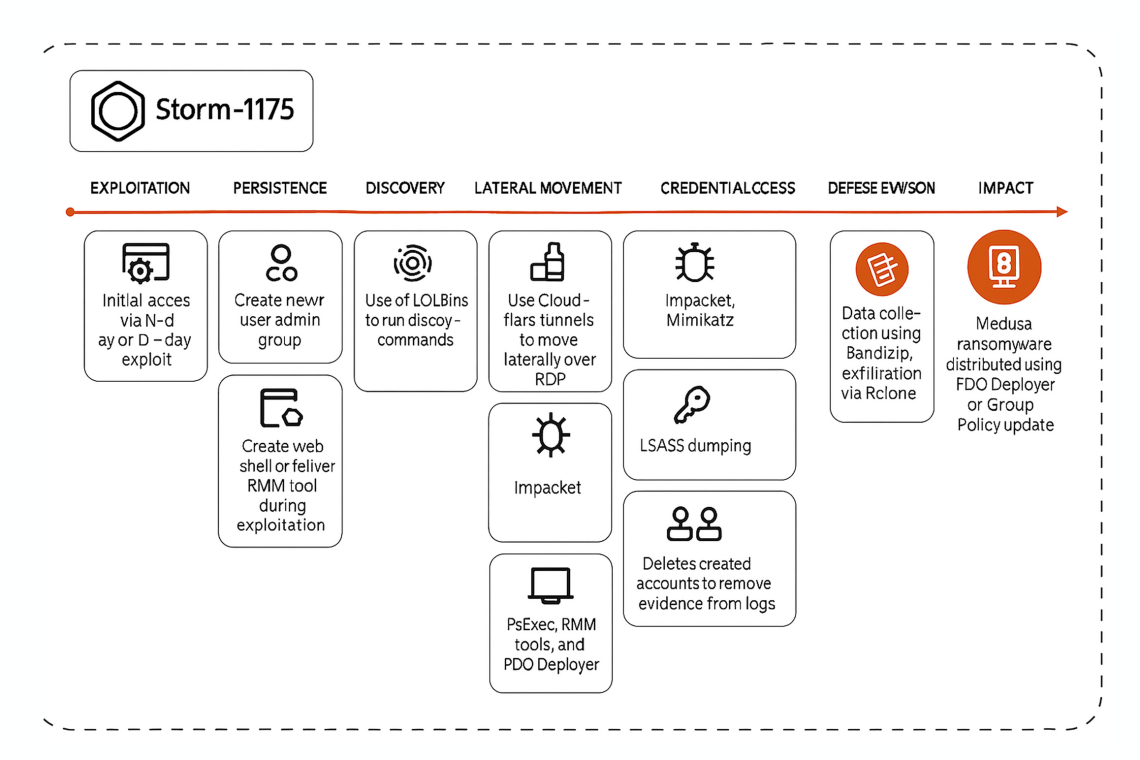
Following initial compromise, Storm‑1175 deploys web shells or remote access tools, creates new administrative accounts for persistence, and moves laterally using a mix of native utilities and remote management software. Commonly abused tools include PowerShell, PsExec, RDP, Cloudflare tunnels, and legitimate remote monitoring and management (RMM) solutions. Software such as PDQ Deployer and frameworks like Impacket are leveraged to propagate access across networks. In many cases, the attackers are able to execute ransomware within a single day.
Credential harvesting plays a central role in their operations. Storm‑1175 uses tools like Impacket and Mimikatz to extract credentials from LSASS, often enabling WDigest to capture plaintext passwords. After achieving elevated access, the group pulls credentials from backups and pivots to domain controllers, enabling access to Active Directory and sensitive system data.
To ensure successful deployment of ransomware, the attackers deliberately undermine endpoint defenses. This includes modifying antivirus configurations, adding exclusions, and disabling protections to prevent detection and blocking of malicious payloads. Data is staged and exfiltrated using utilities such as Rclone, with files compressed prior to transfer.
Microsoft noted that Storm‑1175 tampers with Microsoft Defender Antivirus by altering registry‑stored settings to weaken or disable protections an action that requires highly privileged access. As a result, Microsoft emphasizes the importance of prioritizing alerts related to credential theft and privilege escalation, which often signal an active ransomware intrusion before encryption occurs.
In the final phase of the attack, Storm‑1175 deploys Medusa ransomware across compromised environments using tools like PDQ Deployer or Group Policy, completing the operation.
Microsoft has released indicators of compromise (IoCs) related to these campaigns, along with detailed mitigation recommendations and defensive guidance to help organizations detect and disrupt Storm‑1175 activity.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.