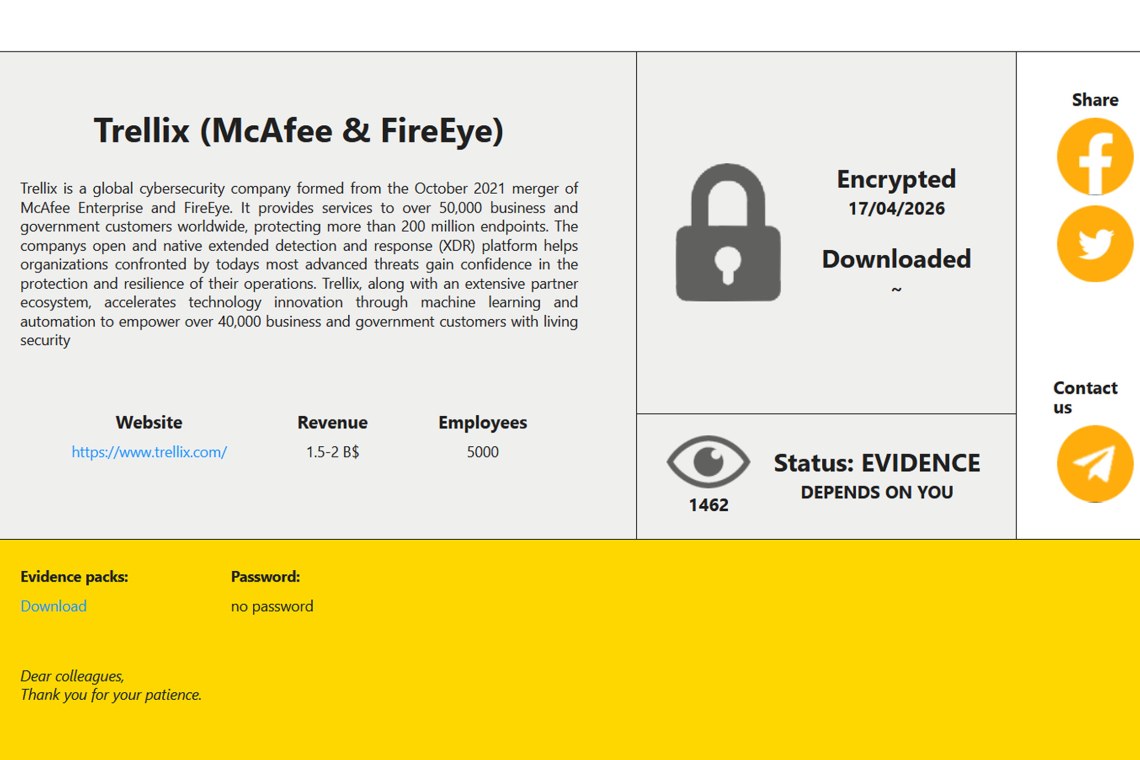
The RansomHouse cyber extortion group has claimed responsibility for a recent security incident involving Trellix, listing the company on its Tor-based leak portal and releasing screenshots that allegedly show access to internal systems.
To support its claims, the group published images that appear to display internal Trellix environments, suggesting that it may have gained unauthorized entry into parts of the company’s infrastructure.
Earlier in May, Trellix disclosed that it had identified a breach affecting a portion of its source code repository. The company responded swiftly by initiating an internal investigation, engaging external forensic specialists, and notifying law enforcement authorities. Although the exact scope of the data exposure has not yet been fully determined, Trellix emphasized that there is currently no indication that its source code has been modified or misused.
In its official statement, the company confirmed that unauthorized access had been detected within part of its repository. However, it also reassured stakeholders that its code release and distribution systems remain unaffected, and there is no evidence to suggest that its products have been compromised as a result of the incident. Trellix noted that it plans to provide further updates once the investigation is complete.
The organization has not publicly attributed the attack to any specific actor or disclosed how the breach occurred. Additionally, the duration of the attacker’s access remains unknown.
Security experts warn that breaches involving source code repositories can expose sensitive internal information, including application logic, APIs, and potentially embedded credentials. Such access can allow threat actors to analyze code for weaknesses, develop targeted exploits, or prepare follow‑on attacks. Beyond immediate risks, these incidents can also result in intellectual property loss, reputational damage, and potential supply chain threats, particularly if altered code is later distributed to customers.
While Trellix has acknowledged unauthorized access, it maintains that there is no current evidence of tampering with its codebase or downstream impact on customers.
About RansomHouse
RansomHouse is a data extortion group that emerged around late 2021 and quickly gained visibility for targeting major organizations worldwide. Unlike traditional ransomware operations that encrypt systems, RansomHouse initially focused on stealing sensitive data and pressuring victims to pay to prevent public disclosure.
Although the group portrays itself as a kind of “mediator” highlighting weak security practices, analysts widely consider it a financially motivated cybercriminal operation. Its campaigns have affected a wide range of sectors, including healthcare, retail, government, and technology organizations. RansomHouse has previously claimed breaches involving companies such as AMD, Shoprite, and several European institutions.
The group’s tactics typically involve exploiting exposed services, weak or reused credentials, phishing campaigns, and vulnerable remote access systems to gain initial entry, followed by data exfiltration and public pressure tactics via leak sites.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.