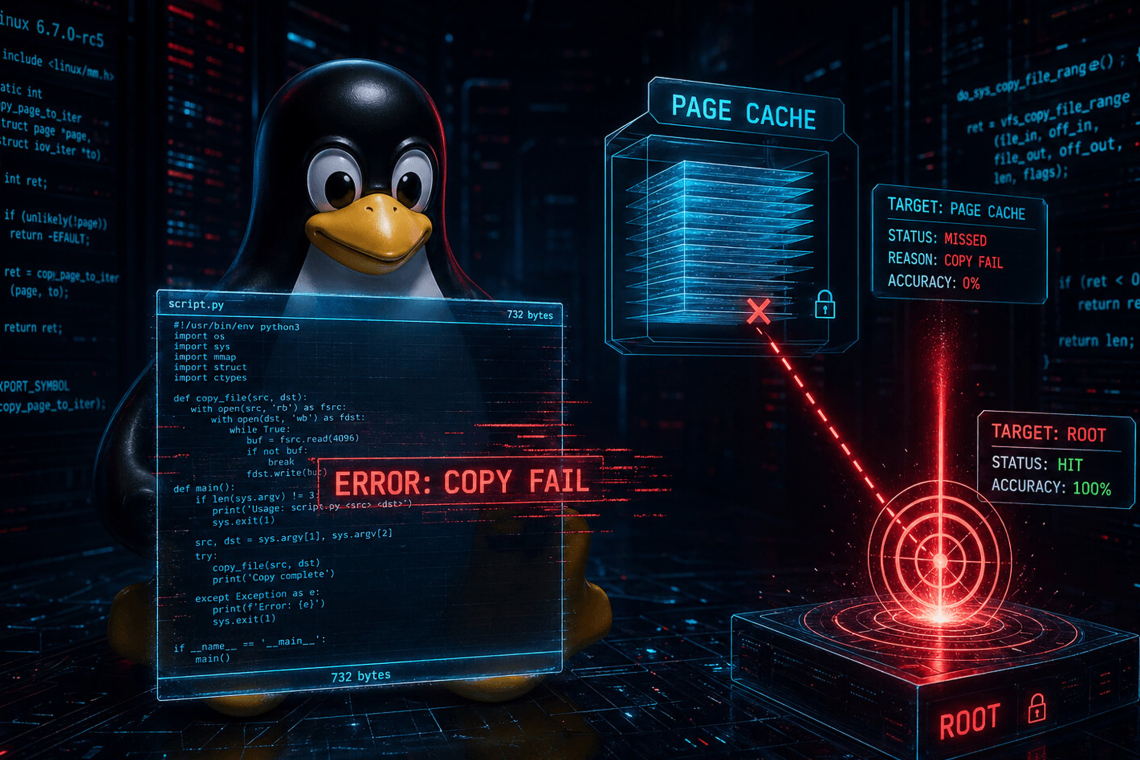
A newly disclosed Linux kernel vulnerability, tracked as CVE‑2026‑31431 and nicknamed “Copy Fail,” allows any local, unprivileged user to corrupt page‑cache data and reliably escalate privileges to root on nearly all modern Linux distributions. The flaw carries a CVSS score of 7.8 and affects systems dating back to 2017.
Researchers from Xint Code describe the issue as a severe logic error that enables an attacker to inject four controlled bytes into the page cache of any file that is readable by the user. Although the modification never touches the file on disk, processes that read the file use the corrupted in‑memory version, making the attack both powerful and difficult to detect.
How the vulnerability works
At a technical level, Copy Fail abuses the interaction between AF_ALG, the Linux kernel’s cryptographic socket interface, and the splice() system call. Together, these components allow attackers to map file‑backed page‑cache memory directly into cryptographic operations. A flaw in the handling of this memory ultimately permits unauthorized writes to cached file contents.
Xint Code explains that a compact exploit implemented as a 732‑byte Python script is sufficient to modify a setuid binary such as /usr/bin/su entirely in memory. Because the underlying file remains unchanged on disk, traditional integrity checks and filesystem monitoring are ineffective at spotting the compromise.
The vulnerability impacts all major distributions, including Ubuntu, Red Hat Enterprise Linux (RHEL), SUSE, and Amazon Linux, and extends beyond bare‑metal systems. Since page cache is shared, a successful attack can cross container boundaries, enabling container escapes and elevating the risk in Kubernetes and multi‑tenant environments.
Nature of the kernel flaw
According to the researchers, Copy Fail stems from a logic error in the kernel’s authencesn AEAD cryptographic template. When triggered, the bug causes corrupted page‑cache data to be left unmarked as “dirty,” meaning the kernel never writes the changes back to disk. While the disk file stays pristine, the in‑memory version used by every process remains silently altered.
As a result, an unprivileged user can manipulate the cached contents of a setuid‑root executable and later execute it to gain full system privileges. The shared nature of the page cache also means that containers relying on the same host kernel can be affected.
Unlike earlier memory corruption vulnerabilities such as Dirty COW or Dirty Pipe, Copy Fail is described as portable, race‑free, and highly stealthy. The exploit does not rely on timing races, large payloads, or unusual kernel configurations and works consistently across architectures and kernel versions tested.
Root cause and exploit chain
The attack path begins with AF_ALG, which exposes the kernel cryptographic subsystem to unprivileged users by design. Attackers bind an AF_ALG socket to the vulnerable authencesn AEAD mode and prepare a cryptographic request.
Using splice(), the attacker maps page‑cache pages from a target file directly into a crypto scatterlist. During an AEAD decryption operation configured to run in‑place, the kernel mixes user‑controlled buffers and file‑backed page‑cache memory in a single writable structure.
The authencesn algorithm violates expected assumptions by using its output buffer as temporary scratch space and writing four bytes past the permitted boundary. In this context, that out‑of‑bounds write lands directly in the page cache of the chosen file. The attacker controls the target file, the offset, and the four‑byte value, allowing precise and repeatable corruption.
Although the cryptographic integrity check fails, the unintended write remains in memory. Repeating this process allows attackers to inject enough shellcode into the cached copy of a privileged binary to redirect execution flow.
Exploitation in practice
The researchers demonstrated the exploit using /usr/bin/su, a standard setuid‑root binary present on most Linux systems:
- The attacker opens and configures an AF_ALG socket bound to the vulnerable authencesn mode.
- Each four‑byte write is staged by placing the desired value in the Associated Authenticated Data (AAD) and using splice() to map the relevant page‑cache offset from the target file.
- A call to
recv()triggers the decryption operation, causing the kernel to perform the faulty scratch write into the page cache. - After enough memory corruption, the attacker executes
execve("/usr/bin/su").
The kernel loads the altered version from page cache rather than disk, and the injected code executes with root privileges.
Xint Code published a demonstration showing the same minimal exploit consistently granting root access to a standard user account on multiple platforms, including Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16. Successful exploitation was confirmed across kernel versions ranging from 6.12 to 6.18.
Scope and impact
The researchers warn that virtually every mainstream Linux system built between 2017 and the release of a patch is affected. No special permissions, kernel debugging features, or network access are required only a local user account. AF_ALG is enabled by default on nearly all distributions, meaning the attack surface is present out of the box.
Copy Fail provides a reliable foundation for local privilege escalation, container escapes, and potential Kubernetes host compromise, making it particularly dangerous for shared and cloud environments.
To aid defenders, Xint Code released a proof‑of‑concept verification tool that allows administrators to check whether their systems remain vulnerable and confirm the effectiveness of vendor patches once applied.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.