Cybersecurity analysts have uncovered a previously undocumented China‑aligned espionage operation aimed at government and defense entities across South, East, and Southeast Asia, with at least one confirmed victim located within a European NATO member state.
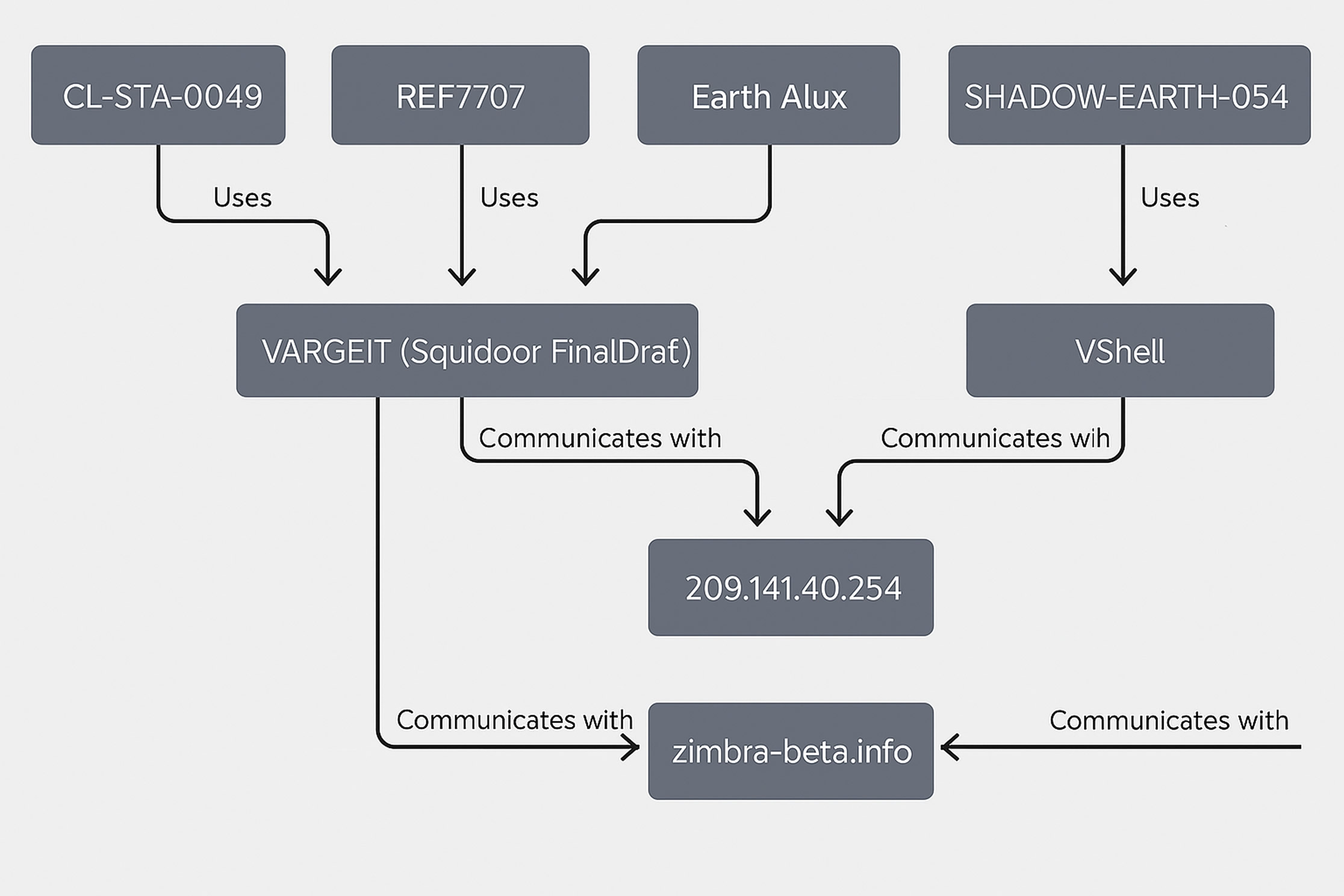
The activity has been attributed by Trend Micro to a threat cluster it temporarily tracks as SHADOW‑EARTH‑053. Researchers believe the group has been operational since at least December 2024 and shows partial infrastructure or operational overlap with other known China‑linked clusters, including CL‑STA‑0049, Earth Alux, and REF7707.
According to Trend Micro researchers Daniel Lunghi and Lucas Silva, the attackers rely heavily on exploiting known (N‑day) vulnerabilities in internet‑exposed Microsoft Exchange and Internet Information Services (IIS) servers. Once access is gained often through exploit chains such as ProxyLogon the group deploys Godzilla web shells to maintain persistent access, followed by the delivery of ShadowPad backdoors using DLL side‑loading techniques that abuse legitimate, digitally signed executables.
Geographic scope and overlap with related clusters
Victims confirmed in the campaign include organizations in Pakistan, Thailand, Malaysia, India, Myanmar, Sri Lanka, and Taiwan. Outside of Asia, Poland is the only European country identified so far in the group’s targeting profile.
Trend Micro observed that nearly half of the organizations compromised by SHADOW‑EARTH‑053 particularly those in Malaysia, Sri Lanka, and Myanmar—had previously been breached by another intrusion set it tracks as SHADOW‑EARTH‑054. Despite the overlap in victimology, the analysts found no evidence of direct operational coordination between the two groups.
Initial access, persistence, and payload delivery
The attacks typically begin with the exploitation of unpatched server‑side vulnerabilities, allowing the attackers to implant web shells that serve as long‑term access points. These shells enable remote command execution and reconnaissance, eventually paving the way for the deployment of ShadowPad malware. In several cases, the payload delivery process leveraged AnyDesk alongside DLL side‑loading to evade detection.
Trend Micro also documented at least one incident involving the exploitation of React2Shell (CVE‑2025‑55182), which was used to distribute a Linux variant of Noodle RAT also known as ANGRYREBEL or Nood RAT. This attack chain was previously associated by Google Threat Intelligence Group (GTIG) with a separate actor tracked as UNC6595.
To establish resilient command‑and‑control channels, the attackers made extensive use of open‑source tunneling tools, including IOX, GO Simple Tunnel (GOST), and wstunnel. To further obscure malicious binaries and evade security solutions, payloads were often packed using RingQ.
Privilege escalation and lateral movement
Once inside a network, SHADOW‑EARTH‑053 employed Mimikatz to harvest credentials and facilitate privilege escalation. Lateral movement was carried out using a custom remote desktop launcher as well as Sharp‑SMBExec, a C#‑based implementation of the SMBExec technique that enables remote command execution across Windows systems.
Trend Micro emphasized that the primary ingress vector for the campaign was vulnerable internet‑facing IIS applications. The company strongly recommends that organizations prioritize applying the latest Microsoft Exchange cumulative updates and ensuring all IIS‑hosted applications are fully patched.
Where immediate patching is not possible, the researchers advise deploying Intrusion Prevention Systems (IPS) or Web Application Firewalls (WAF) configured with rules specifically designed to block exploitation attempts targeting the documented vulnerabilities a mitigation strategy often referred to as virtual patching
Parallel campaigns: Activists and journalists under surveillance
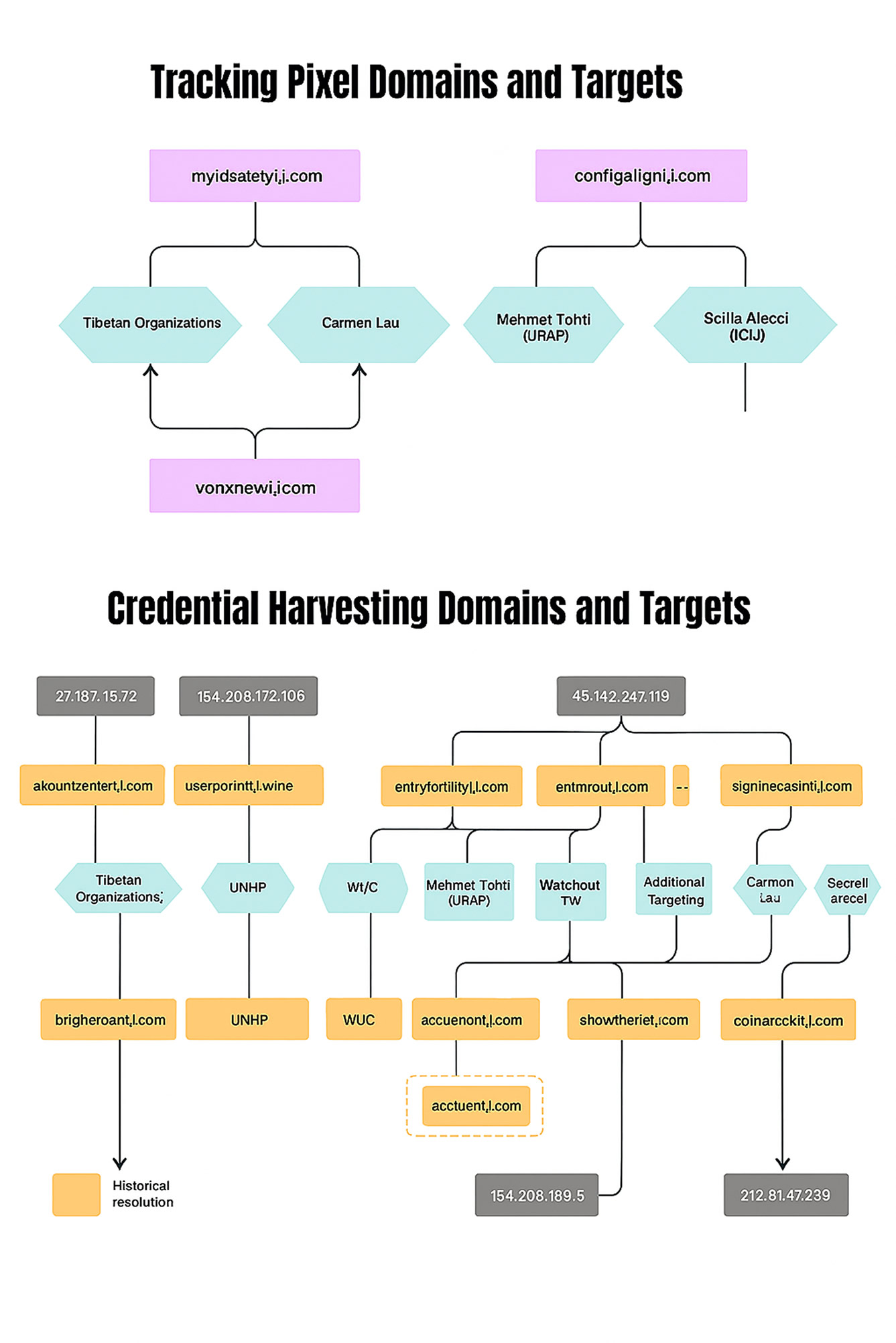
The disclosure coincides with findings from Citizen Lab, which recently identified two separate China‑affiliated phishing campaigns aimed at journalists and civil society organizations. These operations targeted individuals connected to Uyghur, Tibetan, Taiwanese, and Hong Kong diaspora communities, as well as investigative reporters covering issues sensitive to the Chinese government.
The campaigns, first detected in April and June 2025, have been codenamed GLITTER CARP and SEQUIN CARP.
GLITTER CARP primarily targeted the International Consortium of Investigative Journalists (ICIJ), while SEQUIN CARP focused on individual reporters, including ICIJ journalist Scilla Alecci, along with other international journalists covering China‑related issues.
Citizen Lab noted that the attackers relied on carefully crafted impersonation tactics, frequently posing as known individuals or issuing fake security alerts from major technology companies. Despite variations in target selection, both campaigns reused the same supporting infrastructure, domains, and impersonated personas across multiple operations.
GLITTER CARP has also been linked to phishing campaigns against Taiwan’s semiconductor industry, activity that Proofpoint previously documented in July 2025 under the designation UNK_SparkyCarp. SEQUIN CARP also known as UNK_DualTone shares characteristics with a threat actor tracked by Volexity as UTA0388 and an intrusion set Trend Micro refers to as TAOTH.
Objectives and tooling
The central objective of both phishing campaigns is to gain initial access to email accounts, either by harvesting credentials through fraudulent login pages or by tricking victims into granting access via malicious OAuth authorizations. GLITTER CARP emails also embed 1×1 tracking pixels, allowing the attackers to confirm message opens and collect basic device metadata.
Citizen Lab observed that certain organizations were targeted simultaneously using different techniques such as adversary‑in‑the‑middle (AiTM) phishing kits linked to GLITTER CARP alongside separate malware delivery campaigns attributed to UNK_DropPitch. While this overlap suggests shared interests or tooling, the exact relationship between these groups remains unclear.
Attribution and broader implications
Citizen Lab concluded that the campaigns illustrate how digital transnational repression increasingly relies on a decentralized ecosystem of contractors and semi‑independent actors aligned with state intelligence priorities. The targets identified in both GLITTER CARP and SEQUIN CARP match longstanding intelligence interests of the Chinese government.
Based on historical patterns and available evidence, the researchers assess with moderate confidence that commercial entities contracted by the Chinese state may be behind the observed activity.
In a statement to The Hacker News, Mark Kelly, a staff threat researcher at Proofpoint, confirmed that both UNK_SparkyCarp and UNK_DualTone have long engaged in identity‑based phishing campaigns across a wide range of sectors. He described the targeting of civil society figures as consistent with the groups’ historical behavior rather than a recent escalation.
Kelly noted that Proofpoint has observed UNK_SparkyCarp targeting academic, political, semiconductor, and legal sectors across the United States, Europe, and Taiwan. He added that Proofpoint visibility limitations likely explain why not all civil society targeting was previously observed, and said the firm agrees with Citizen Lab’s attribution.
Proofpoint further reported detecting UNK_DualTone activity against multiple U.S. journalists in May 2025, using phishing lures tied to protests planned around the U.S. Army’s 250th Anniversary Parade, reinforcing concerns about the continued expansion of influence‑driven cyber operations.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.