Censys researchers have identified 5,219 publicly exposed Rockwell Automation programmable logic controllers (PLCs) across the internet, the majority of which are located in the United States. The findings reinforce recent government warnings and prompted calls for organizations to secure or disconnect vulnerable devices.
On April 7, 2026, U.S. authorities including the FBI, CISA, and NSA issued an alert warning that Iran‑linked advanced persistent threat (APT) actors are actively exploiting internet‑accessible Rockwell Automation PLCs. The campaign targets operational technology (OT) environments across multiple critical infrastructure sectors.
According to the advisory, the threat activity is aimed at disrupting essential services, including government operations, water systems, and energy infrastructure. The attacks involve tampering with PLC project files and manipulating data displayed on human‑machine interface (HMI) and SCADA systems, in some cases resulting in operational interruptions and financial damage. Investigators have linked the activity to Iran‑associated groups such as CyberAv3ngers, which has ties to Iran’s Islamic Revolutionary Guard Corps (IRGC).
Authorities are urging organizations to identify exposed OT assets, follow vendor‑recommended security guidance, remove systems from direct internet access whenever possible, and coordinate with government agencies for incident response and mitigation assistance.
Censys’ independent analysis found 5,219 exposed Rockwell Automation PLCs worldwide, with 74.6% located in the United States. Many of these systems appear to be connected through cellular networks, suggesting deployment in remote or field environments. Researchers also noted that multiple IP addresses may be associated with a single compromised engineering workstation, indicating a broader attack surface than initially reported.
“Censys identifies 5,219 internet‑exposed hosts globally responding on EtherNet/IP (port 44818) that self‑identify as Rockwell Automation/Allen‑Bradley devices,” the report states. “The geographic distribution is heavily skewed toward the United States, accounting for nearly three‑quarters of global exposure, consistent with Rockwell’s dominant role in North American industrial automation.”
While the U.S. represents the largest concentration, exposed devices were also observed in Spain, Taiwan, and Italy, with Iceland showing an unusually high level of exposure relative to its size. Censys noted that many of the systems rely on cellular providers such as Verizon and AT&T, and in some cases satellite connectivity, indicating deployment in utilities, substations, and other remote facilities where patching and monitoring can be more challenging.
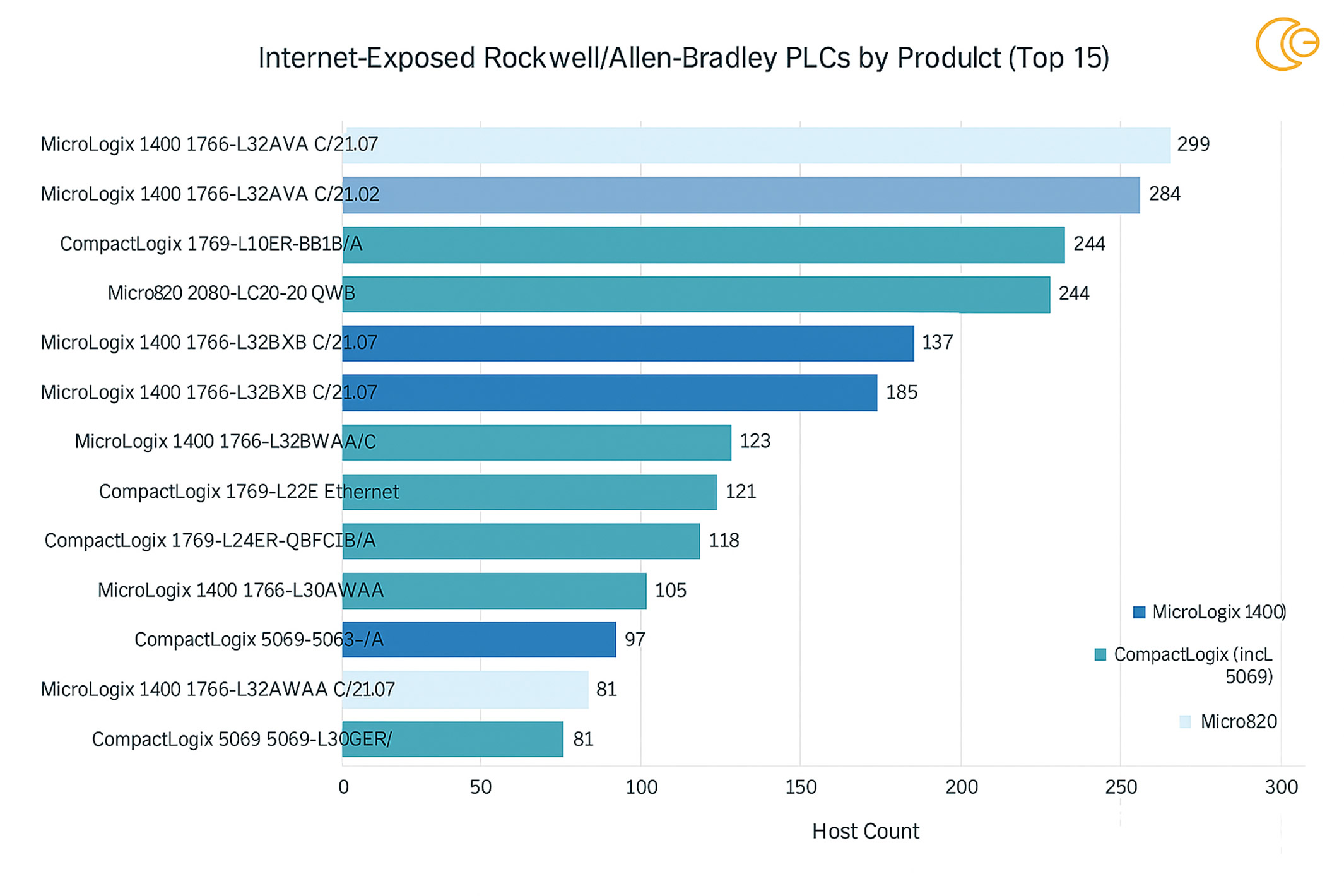
The majority of exposed PLCs belong to the MicroLogix and CompactLogix product families, many of which are running outdated firmware versions.
“EtherNet/IP identity responses reveal device‑level product strings, allowing attackers to fingerprint PLC models and firmware revisions without authentication,” the report explains. “The fifteen most common product identifiers are dominated by MicroLogix 1400 devices (1766‑ prefix) and CompactLogix systems (1769‑ and 5069‑ prefixes), with a smaller number of Micro820 devices (2080‑).”
Because these device details can be collected remotely without credentials, attackers can easily scan, classify, and prioritize vulnerable systems significantly increasing the risk to sectors such as energy, manufacturing, and water infrastructure.
Censys further found that many of the exposed PLCs are running additional services beyond EtherNet/IP, which further expands the attack surface. These include VNC for remote HMI access, Telnet for legacy plaintext access, Modbus for industrial communications, and Red Lion Crimson software commonly used in mixed‑vendor OT environments. Each exposed service introduces additional pathways for compromise and lateral movement.
The report also includes indicators of compromise (IOCs) and technical details related to the observed attacker infrastructure to support detection and defensive efforts.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.


