A recently disclosed critical security vulnerability affecting nginx‑ui, an open‑source web‑based management interface for Nginx, is now being actively exploited in the wild, exposing unpatched environments to immediate takeover risks.
The flaw, tracked as CVE‑2026‑33032 and rated 9.8 on the CVSS severity scale, allows attackers to bypass authentication controls and gain full administrative control over the Nginx service. Security researchers at Pluto Security have dubbed the issue “MCPwn” due to its abuse of nginx‑ui’s Model Context Protocol (MCP) integration.
Root Cause and Technical Details
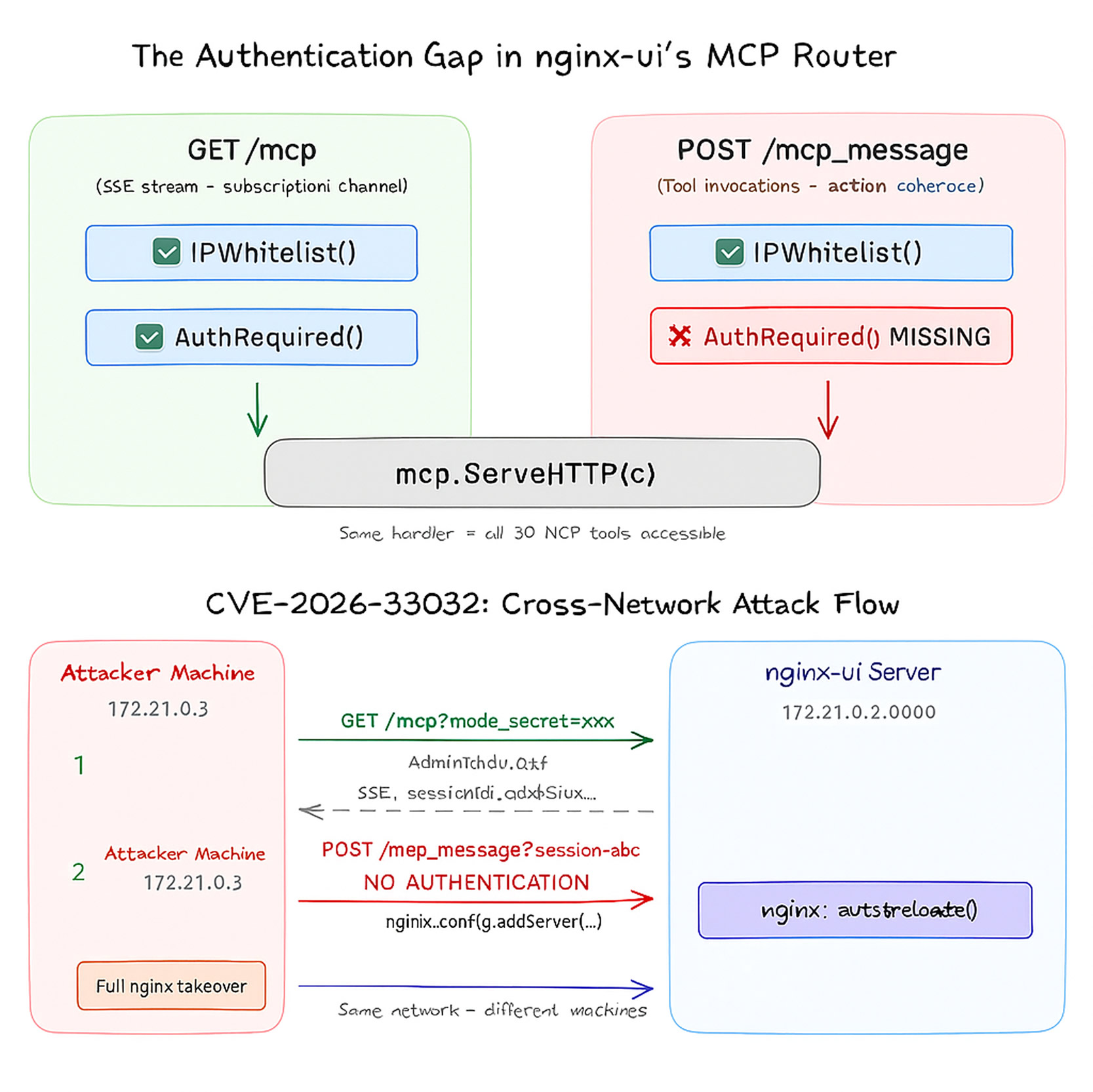
According to an advisory published by the nginx‑ui maintainers last month, the vulnerability originates from inconsistent authentication enforcement across two MCP‑related HTTP endpoints:
/mcp/mcp_message
While the /mcp endpoint correctly enforces both IP allowlisting and authentication via the AuthRequired() middleware, the /mcp_message endpoint only applies IP allowlisting. Critically, nginx‑ui ships with an empty default IP allowlist, which the middleware interprets as “allow all”.
As a result, any attacker with network access can interact with the /mcp_message endpoint without providing credentials, effectively bypassing all authentication mechanisms.
“This means any network attacker can invoke all MCP tools without authentication,” the advisory warned, “including restarting Nginx, creating, modifying, or deleting Nginx configuration files, and triggering configuration reloads resulting in complete control of the Nginx service.”
Exploitation Mechanics
Pluto Security researcher Yotam Perkal, who discovered and responsibly disclosed the issue, demonstrated that a full takeover can be achieved in seconds using only two HTTP requests:
- Send an HTTP GET request to the
/mcpendpoint to establish a session and obtain a session identifier. - Issue an HTTP POST request to the
/mcp_messageendpoint using the session ID to invoke any MCP tool—without authentication.
In practice, attackers can skip authentication entirely by crafting direct requests to /mcp_message, omitting tokens or authorization headers altogether.
Impact and Risk
Successful exploitation allows threat actors to:
- Modify or replace Nginx configuration files
- Reload or restart the Nginx service at will
- Intercept and manipulate all inbound and outbound traffic
- Potentially harvest administrator credentials
- Establish persistence and move laterally within the environment
This effectively grants attackers full control of affected Nginx servers, making the vulnerability particularly severe for internet‑facing deployments.
Mitigation and Fixes
Following responsible disclosure, the issue was resolved in nginx‑ui version 2.3.4, released on March 15, 2026.
For environments unable to upgrade immediately, maintainers recommend the following interim mitigations:
- Add
middleware.AuthRequired()to the/mcp_messageendpoint to enforce authentication - Change the default IP allowlist behavior from “allow‑all” to “deny‑all”
- Restrict access to nginx‑ui using network‑level controls such as firewalls or VPNs
Active Exploitation and Exposure
The disclosure coincides with a report published this week by Recorded Future, which identified CVE‑2026‑33032 as one of 31 vulnerabilities actively exploited by threat actors in March 2026. While detailed exploitation telemetry has not yet been released publicly, the inclusion underscores the immediacy of the threat.
“When MCP is bolted onto an existing application, it inherits all of the application’s capabilities but not necessarily its security controls,” Perkal explained. “The result is effectively a backdoor that bypasses every authentication safeguard the application was designed to enforce.”
Internet‑wide scanning data from Shodan indicates approximately 2,689 nginx‑ui instances are currently exposed, with the highest concentrations observed in China, the United States, Indonesia, Germany, and Hong Kong.
“Given the roughly 2,600 publicly accessible nginx‑ui deployments we’ve identified, the risk to unpatched systems is immediate,” Pluto Security told The Hacker News. “Organizations should treat this as an emergency upgrade immediately, or disable MCP functionality and restrict access until remediation is complete.”
Related MCP Risks
The nginx‑ui findings follow closely behind the discovery of two critical vulnerabilities in Atlassian’s MCP server (mcp‑atlassian) that can be chained to achieve unauthenticated remote code execution. Tracked as CVE‑2026‑27825 (CVSS 9.1) and CVE‑2026‑27826 (CVSS 8.2) and collectively dubbed MCPwnfluence, the flaws allow attackers on the same local network to execute arbitrary code without authentication.
“When chained together, the vulnerabilities enable an attacker to redirect the MCP server, upload malicious content, and achieve full unauthenticated RCE from the local network,” Pluto Security said.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.


